Configuring Advanced Firewall settings
Description
Configuring Advanced Firewall Settings
Resolution for SonicOS 7.X
This release includes significant user interface changes and many new features that are different from the SonicOS 6.5 and earlier firmware. The below resolution is for customers using SonicOS 7.X firmware.
To configure advanced firewall settings, navigate to Network | System | Firewall | Advanced tab.
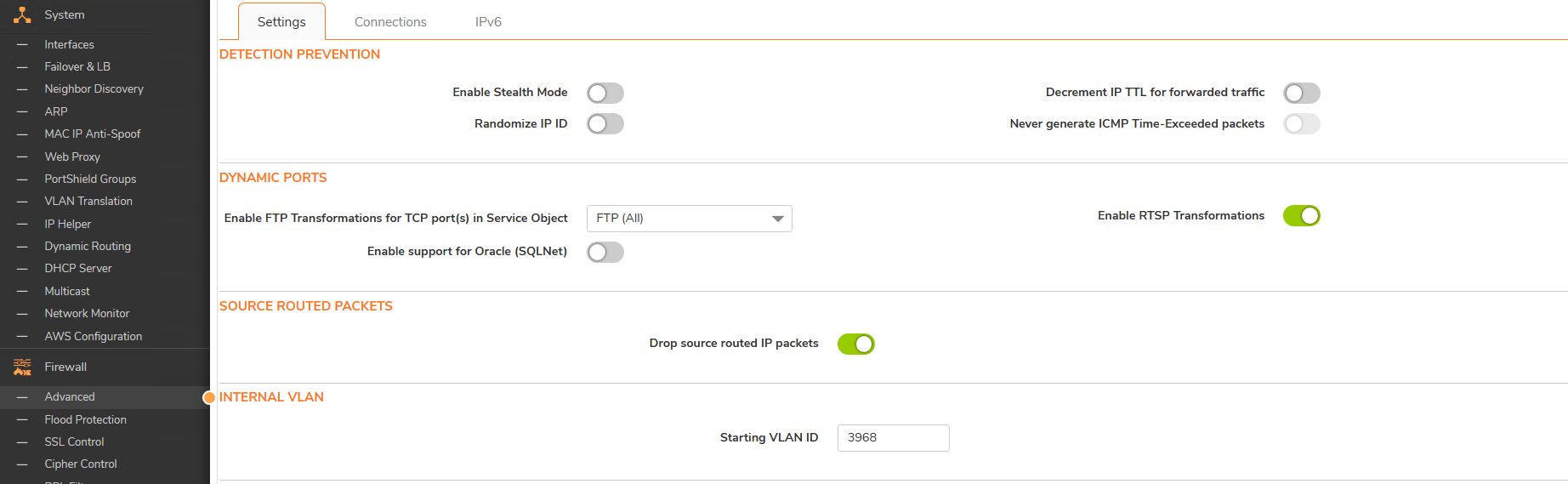
Detection Prevention
- Enable Stealth Mode - By default, the security appliance responds to incoming connection requests as either "blocked" or "open." If you enable Stealth Mode, your security appliance does not respond to blocked inbound connection requests. Stealth Mode makes your security appliance essentially invisible to hackers.
- Randomize IP ID - Select Randomize IP ID to prevent hackers using various detection tools from detecting the presence of a security appliance. IP packets are given random IP IDs, which makes it more difficult for hackers to "fingerprint" the security appliance.
- Decrement IP TTL for forwarded traffic - Time-to-live (TTL) is a value in an IP packet that tells a network router whether or not the packet has been in the network too long and should be discarded. Select this option to decrease the TTL value for packets that have been forwarded and therefore have already been in the network for some time.
- Never generate ICMP Time-Exceeded packets - The SonicWall appliance generates Time-Exceeded packets to report when it has dropped a packet because its TTL value has decreased to zero. Select this option if you do not want the SonicWall appliance to generate these reporting packets.
Dynamic Ports
- Enable FTP Transformations for TCP port(s) in Service Object FTP operates on TCP ports 20 and 21 where port 21 is the Control Port and 20 is Data Port. However, when using nonstandard ports (eg. 2020, 2121), SonicWall drops the packets by default as it is not able to identify it as FTP traffic. The Enable FTP Transformations for TCP port(s) in Service Object option allows you to select a Service Object to specify a custom control port for FTP traffic.
- To illustrate how this feature works, consider the following example of an FTP server behind the SonicWall listening on port 2121.
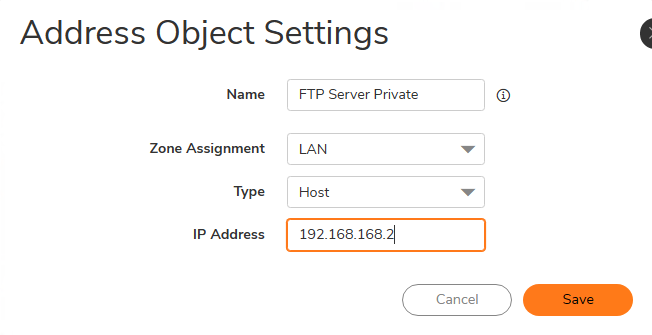
- On the Object |Match Objects | Addresses page, create an Address Object by clicking Add for the private IP address of the FTP server with the following values.
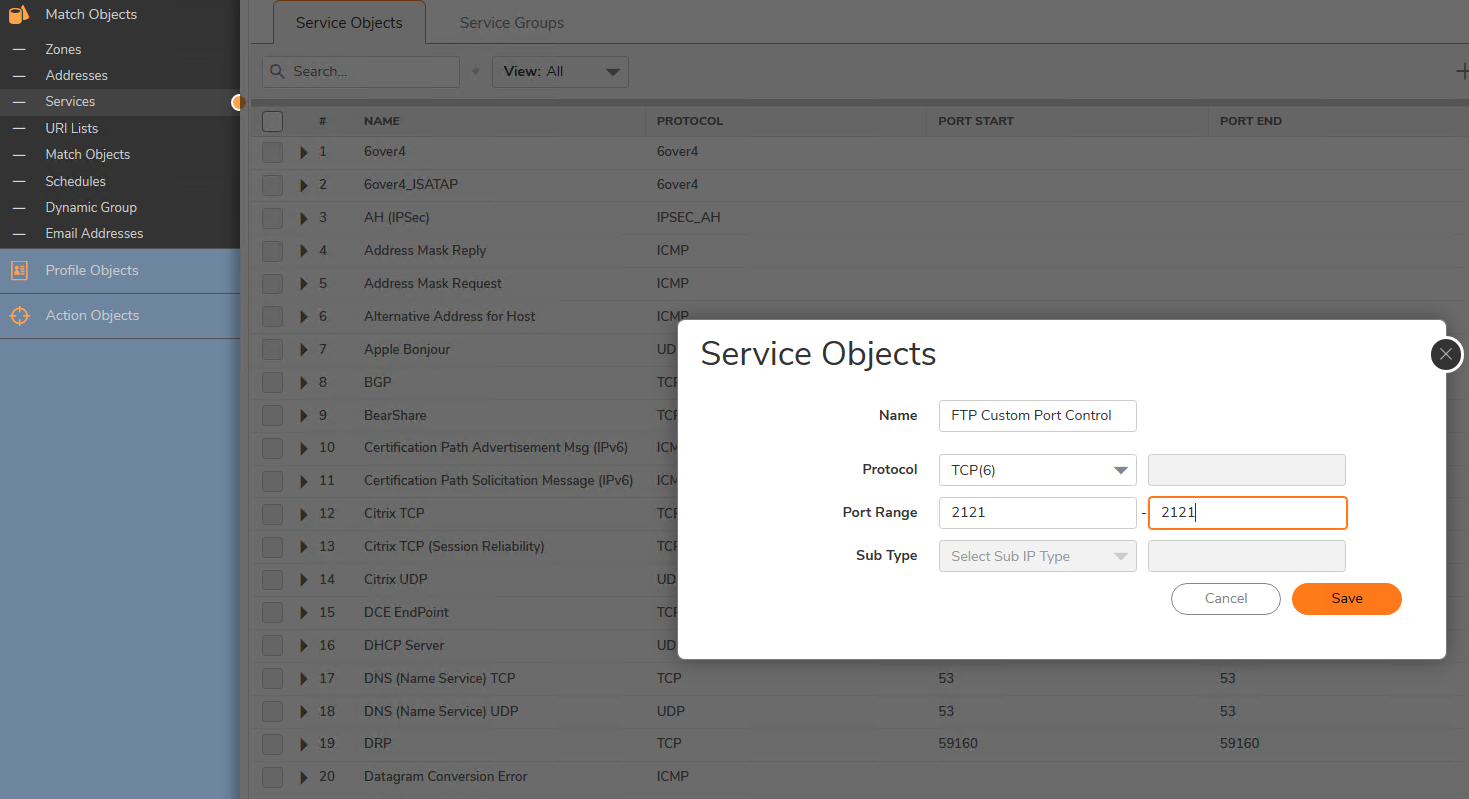
- On the Object |Match Objects | Services page, create a custom Service by clicking Add for the FTP Server with the following values:
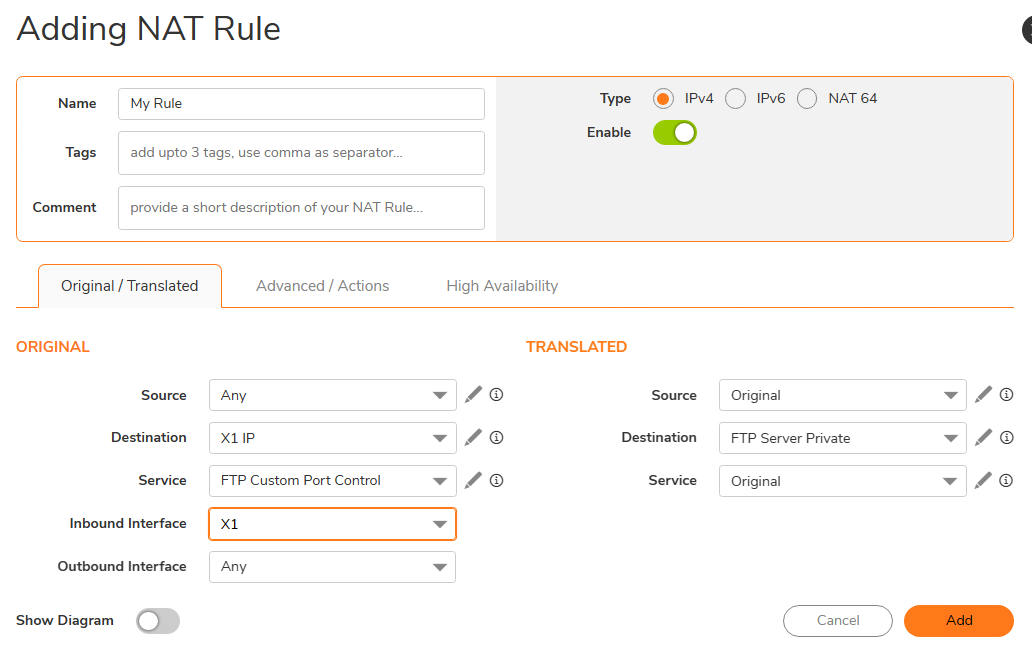
- On the Network | Policies | Rules and policies | NAT rules page, create the following NAT Policy.
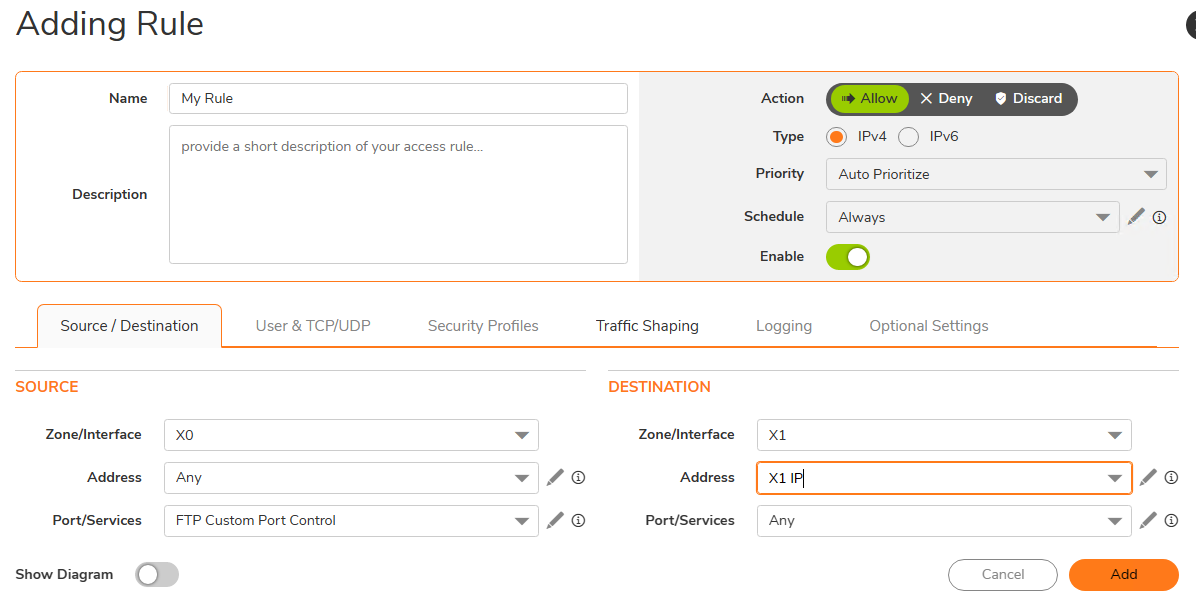
- On the Network | Policies | Rules and policies | Access rules page, create the following Access Rule.
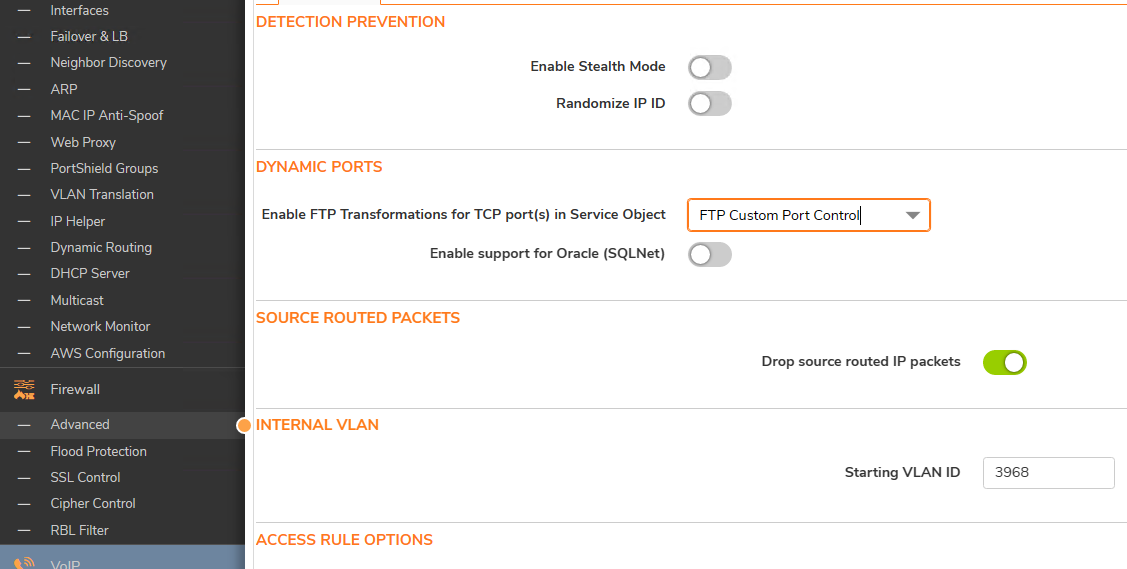
- Lastly, on the Network | Firewall | Advanced page, for the Enable FTP Transformations for TCP port(s) in Service Object select the FTP Custom Port Control Service Object.
- The following options are also configured in the Dynamic Ports section of the Firewall Settings | Advanced page:
- Enable support for Oracle (SQLNet) - Select if you have Oracle applications on your network.
- Enable RTSP Transformations - Select this option to support on-demand delivery of Real time data, such as audio and video. RTSP (Real Time Streaming Protocol) is an application level protocol for control over delivery of data with real-time properties.
Source Routed Packets
- Drop Source Routed Packets - (Enabled by default.) Clear this check box if you are testing traffic between two specific hosts and you are using source routing.
Connections
The Connections section provides the ability to fine-tune the performance of the appliance to prioritize either optimal performance or support for an increased number of simultaneous connections that are inspected by firewall services. There is no change in the level of security protection provided by either of the DPI Connections settings below. The following connection options are available:
- Maximum SPI Connections (DPI services disabled) - This option does not provide SonicWall DPI Security Services protection and optimizes the firewall for maximum number of connections with only Stateful packet inspection enabled.
- Maximum DPI Connections (DPI services enabled) - This is the default and recommended setting for most SonicWall deployments.
- DPI Connections (DPI services enabled with additional performance optimization) - This option is intended for performance critical deployments. This option trades off the number of maximum DPI connections for an increased firewall DPI inspection throughput.
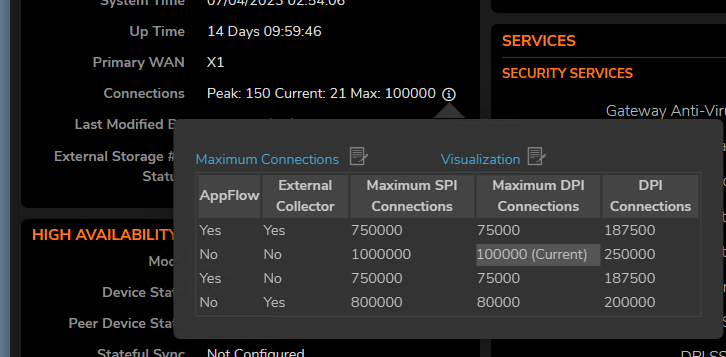
The maximum number of connections also depends on whether App Flow is enabled and if an external collector is configured, as well as the physical capabilities of the particular model of SonicWall security appliance. Mousing over the question mark icon next to the Connections heading displays a pop-up table of the maximum number of connections for your specific SonicWall security appliance for the various configuration permutations. The
table entry for your current configuration is indicated in the table, as shown in the example below.
Access Rule Service Options
- Force inbound and outbound FTP data connections to use default port 20 - The default configuration allows FTP connections from port 20 but remaps outbound traffic to a port such as 1024. If the check box is selected, any FTP data connection through the security appliance must come from port 20 or the connection is dropped. The event is then logged as a log event on the security appliance.
- Apply firewall rules for intra-LAN traffic to/from the same interface - Applies firewall rules that is received on a LAN interface and that is destined for the same LAN interface. Typically, this only necessary when secondary LAN subnets are configured.
- IP and UDP Checksum Enforcement:
- Enable IP header checksum enforcement - Select this to enforce IP header checksums.
- Enable UDP checksum enforcement - Select this to enforce IP header checksums.
IPv6 Advanced Configuration
- Drop IPv6 Routing Header type 0 packets V Select this to prevent a potential DoS attack that exploits IPv6 Routing Header type 0 (RH0) packets. When this setting is enabled, RH0 packets are dropped unless their destination is the SonicWall security appliance and their Segments Left value is 0. Segments Left specifies the number of route segments remaining before reaching the final destination.
Resolution for SonicOS 6.5
This release includes significant user interface changes and many new features that are different from the SonicOS 6.2 and earlier firmware. The below resolution is for customers using SonicOS 6.5 firmware.
To configure advanced firewall settings, navigate to Manage | Firewall Settings | Advanced tab.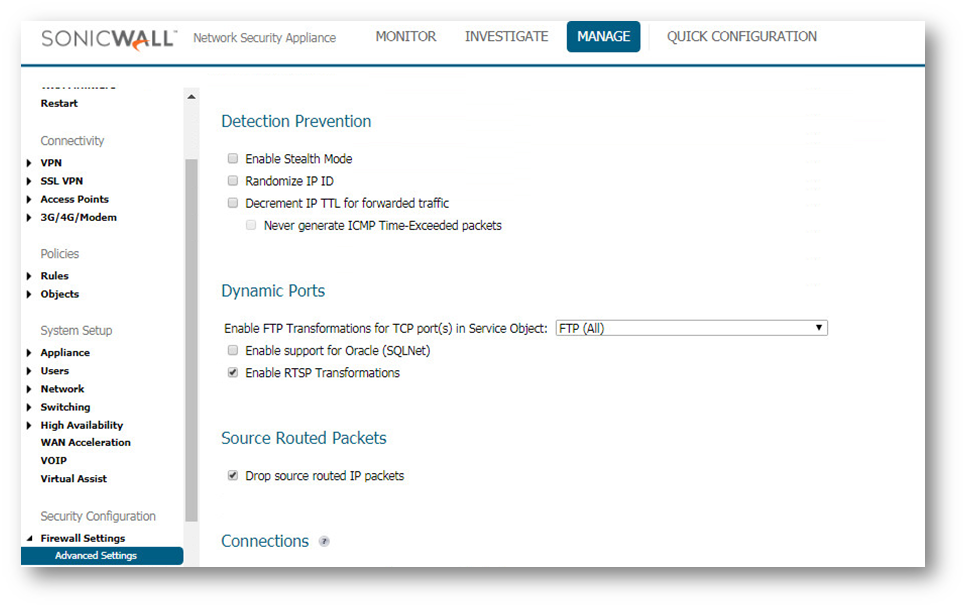
Detection Prevention
- Enable Stealth Mode - By default, the security appliance responds to incoming connection requests as either "blocked" or "open." If you enable Stealth Mode, your security appliance does not respond to blocked inbound connection requests. Stealth Mode makes your security appliance essentially invisible to hackers.
- Randomize IP ID - Select Randomize IP ID to prevent hackers using various detection tools from detecting the presence of a security appliance. IP packets are given random IP IDs, which makes it more difficult for hackers to "fingerprint" the security appliance.
- Decrement IP TTL for forwarded traffic - Time-to-live (TTL) is a value in an IP packet that tells a network router whether or not the packet has been in the network too long and should be discarded. Select this option to decrease the TTL value for packets that have been forwarded and therefore have already been in the network for some time.
- Never generate ICMP Time-Exceeded packets - The SonicWall appliance generates Time-Exceeded packets to report when it has dropped a packet because its TTL value has decreased to zero. Select this option if you do not want the SonicWall appliance to generate these reporting packets.
Dynamic Ports
- Enable FTP Transformations for TCP port(s) in Service Object FTP operates on TCP ports 20 and 21 where port 21 is the Control Port and 20 is Data Port. However, when using nonstandard ports (eg. 2020, 2121), SonicWall drops the packets by default as it is not able to identify it as FTP traffic. The Enable FTP Transformations for TCP port(s) in Service Object option allows you to select a Service Object to specify a custom control port for FTP traffic.
- To illustrate how this feature works, consider the following example of an FTP server behind the SonicWall listening on port 2121.
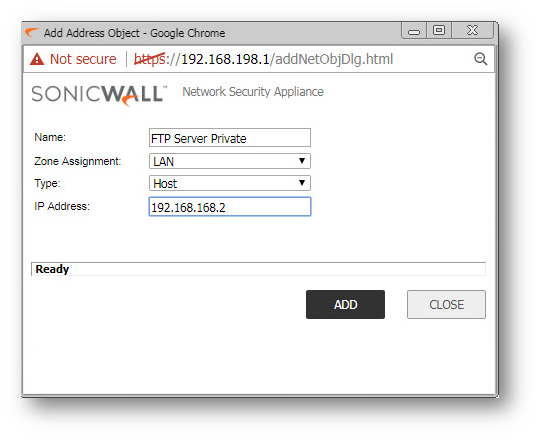
- On the Manage | Objects | Address Objects page, create an Address Object by clicking Add for the private IP address of the FTP server with the following values.
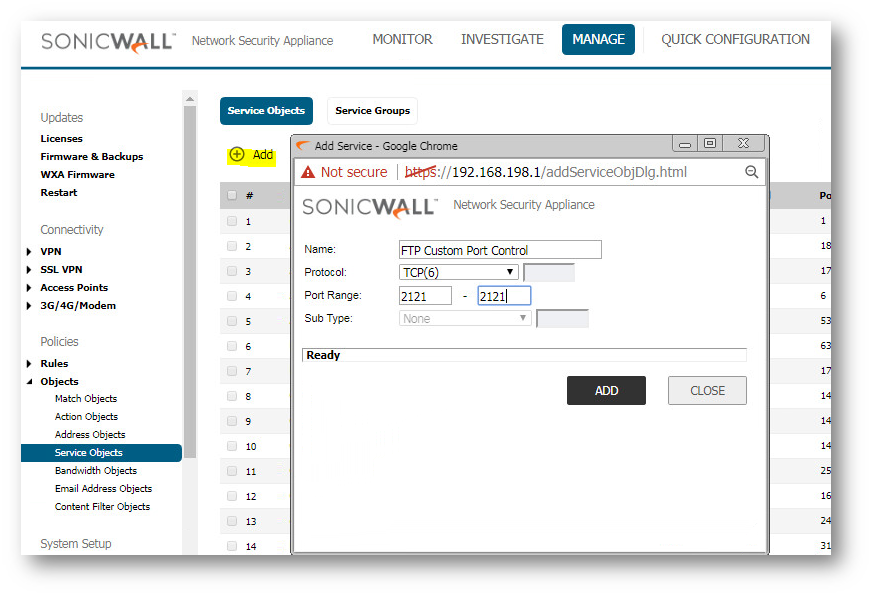
- On the Manage | Network | Service Objects page, create a custom Service by clicking Add for the FTP Server with the following values:
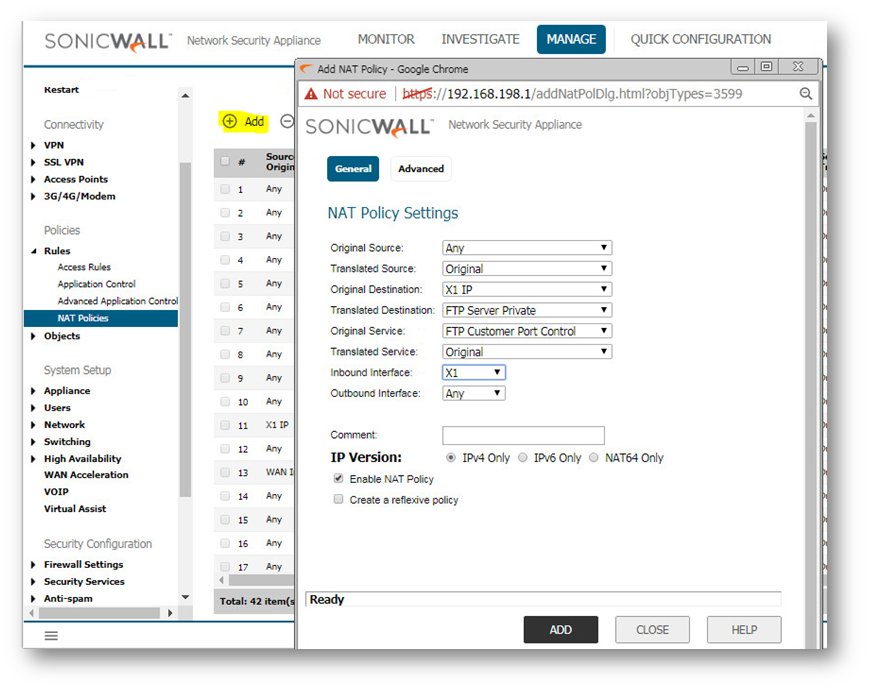
- On the Manage | Rules | NAT Policies page, create the following NAT Policy.
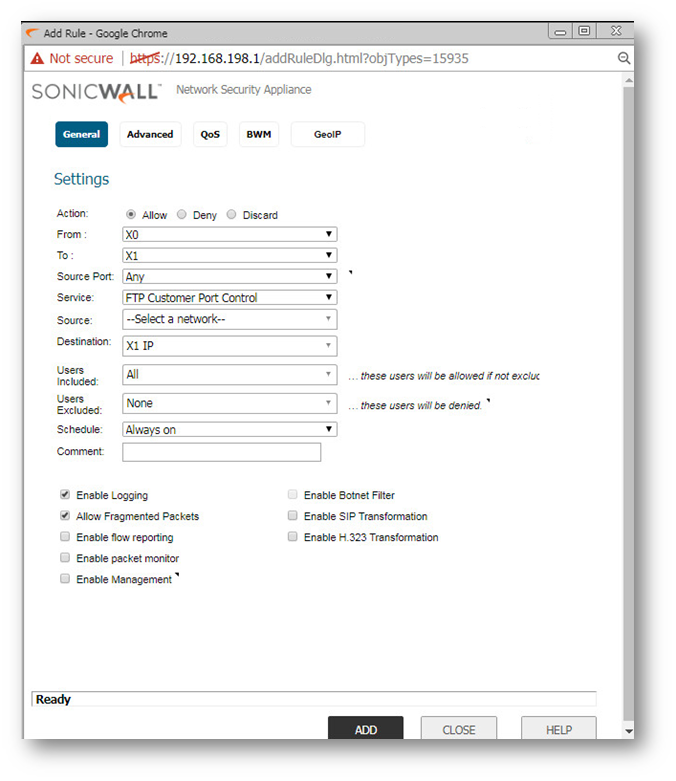
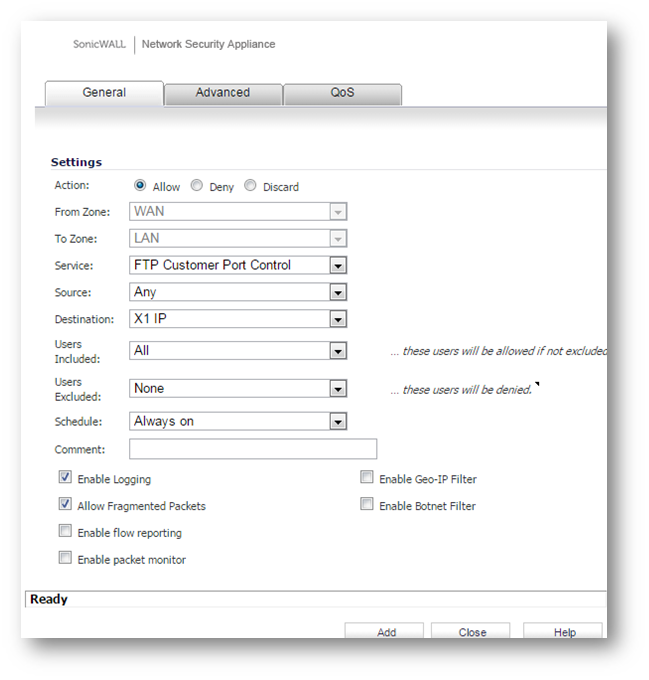
- On the Manage | Rules | Access Rules page, create the following Access Rule.
- Lastly, on the Manage | Firewall Settings | Advanced page, for the Enable FTP Transformations for TCP port(s) in Service Object select the FTP Custom Port Control Service Object.
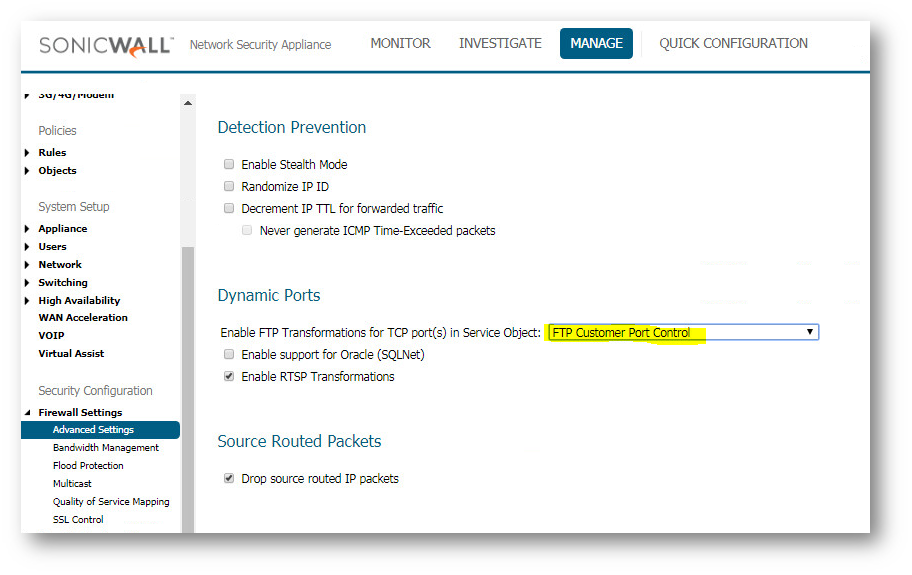
- The following options are also configured in the Dynamic Ports section of the Firewall Settings | Advanced page:
- Enable support for Oracle (SQLNet) - Select if you have Oracle applications on your network.
- Enable RTSP Transformations - Select this option to support on-demand delivery of Real time data, such as audio and video. RTSP (Real Time Streaming Protocol) is an application level protocol for control over delivery of data with real-time properties.
Source Routed Packets
- Drop Source Routed Packets - (Enabled by default.) Clear this check box if you are testing traffic between two specific hosts and you are using source routing.
Connections
The Connections section provides the ability to fine-tune the performance of the appliance to prioritize either optimal performance or support for an increased number of simultaneous connections that are inspected by firewall services. There is no change in the level of security protection provided by either of the DPI Connections settings below. The following connection options are available:
- Maximum SPI Connections (DPI services disabled) - This option does not provide SonicWall DPI Security Services protection and optimizes the firewall for maximum number of connections with only Stateful packet inspection enabled.
- Maximum DPI Connections (DPI services enabled) - This is the default and recommended setting for most SonicWall deployments.
- DPI Connections (DPI services enabled with additional performance optimization) - This option is intended for performance critical deployments. This option trades off the number of maximum DPI connections for an increased firewall DPI inspection throughput.
The maximum number of connections also depends on whether App Flow is enabled and if an external collector is configured, as well as the physical capabilities of the particular model of SonicWall security appliance. Mousing over the question mark icon next to the Connections heading displays a pop-up table of the maximum number of connections for your specific SonicWall security appliance for the various configuration permutations. The
table entry for your current configuration is indicated in the table, as shown in the example below.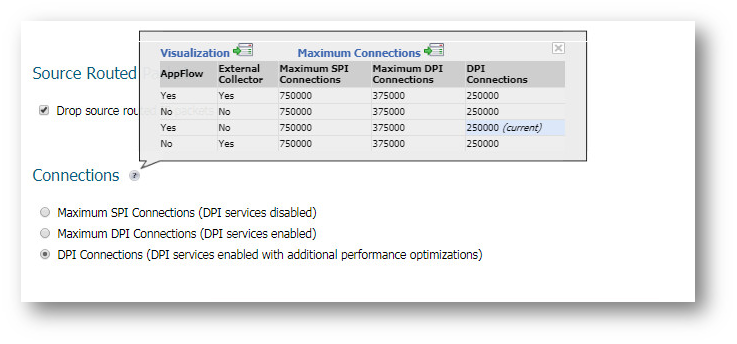
Access Rule Service Options
- Force inbound and outbound FTP data connections to use default port 20 - The default configuration allows FTP connections from port 20 but remaps outbound traffic to a port such as 1024. If the check box is selected, any FTP data connection through the security appliance must come from port 20 or the connection is dropped. The event is then logged as a log event on the security appliance.
- Apply firewall rules for intra-LAN traffic to/from the same interface - Applies firewall rules that is received on a LAN interface and that is destined for the same LAN interface. Typically, this only necessary when secondary LAN subnets are configured.
- IP and UDP Checksum Enforcement:
- Enable IP header checksum enforcement - Select this to enforce IP header checksums.
- Enable UDP checksum enforcement - Select this to enforce IP header checksums.
IPv6 Advanced Configuration
- Drop IPv6 Routing Header type 0 packets V Select this to prevent a potential DoS attack that exploits IPv6 Routing Header type 0 (RH0) packets. When this setting is enabled, RH0 packets are dropped unless their destination is the SonicWall security appliance and their Segments Left value is 0. Segments Left specifies the number of route segments remaining before reaching the final destination.
Resolution for SonicOS 6.2 and Below
The below resolution is for customers using SonicOS 6.2 and earlier firmware. For firewalls that are generation 6 and newer we suggest to upgrade to the latest general release of SonicOS 6.5 firmware.
To configure advanced firewall settings, navigate to Firewall Settings | Advanced tab.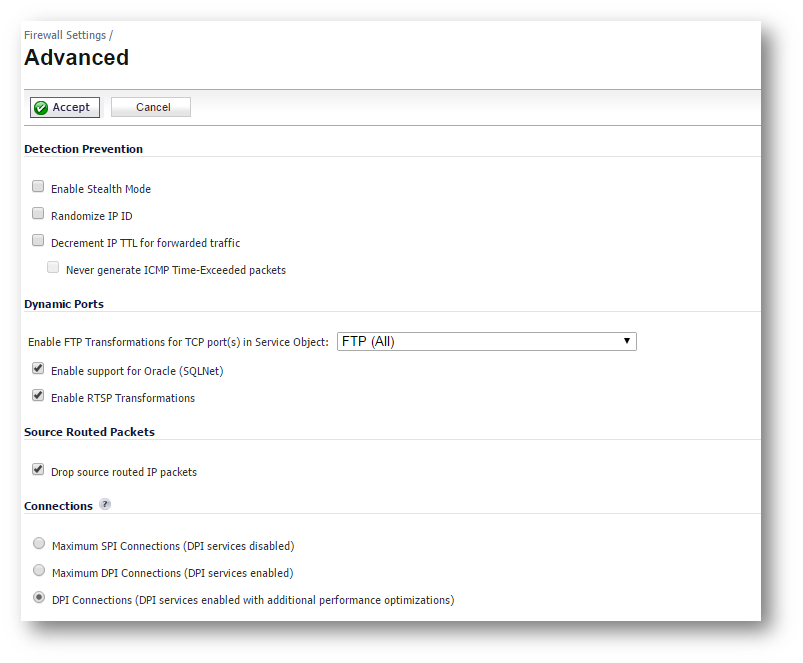
Detection Prevention
- Enable Stealth Mode - By default, the security appliance responds to incoming connection requests as either blocked or open. If you enable Stealth Mode, your security appliance does not respond to blocked inbound connection requests. Stealth Mode makes your security appliance essentially invisible to hackers.
- Randomize IP ID - Select Randomize IP ID to prevent hackers using various detection tools from detecting the presence of a security appliance. IP packets are given random IP IDs, which makes it more difficult for hackers to "fingerprint" the security appliance.
- Decrement IP TTL for forwarded traffic - Time-to-live (TTL) is a value in an IP packet that tells a network router whether or not the packet has been in the network too long and should be discarded. Select this option to decrease the TTL value for packets that have been forwarded and therefore have already been in the network for some time.
- Never generate ICMP Time-Exceeded packets - The SonicWall appliance generates Time-Exceeded packets to report when it has dropped a packet because its TTL value has decreased to zero. Select this option if you do not want the SonicWall appliance to generate these reporting packets.
Dynamic Ports
- Enable FTP Transformations for TCP port(s) in Service Object FTP operates on TCP ports 20 and 21 where port 21 is the Control Port and 20 is Data Port. However, when using nonstandard ports (eg. 2020, 2121), SonicWall drops the packets by default as it is not able to identify it as FTP traffic. The Enable FTP Transformations for TCP port(s) in Service Object option allows you to select a Service Object to specify a custom control port for FTP traffic.
- To illustrate how this feature works, consider the following example of an FTP server behind the SonicWall listening on port 2121.
- On the Network | Address Objects page, create an Address Object for the private IP address of the FTP server with the following values.
Name: FTP Server Private
Zone: LAN
Type: Host
IP Address: 192.168.168.2 - On the Network | Services page, create a custom Service for the FTP Server with the following values.
Name: FTP Custom Port Control
Protocol: TCP(6)
Port Range: 2121 - 2121 - On the Network | NAT Policies page, create the following NAT Policy, and on the Firewall Settings | Advanced page, create the following access rule.
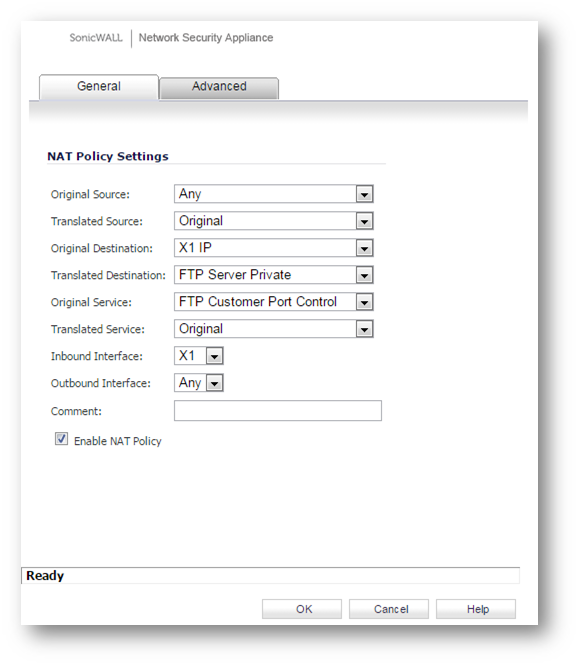
- Lastly, on the Firewall Settings | Advanced page, for the Enable FTP Transformations for TCP port(s) in Service Object select the FTP Custom Port Control Service Object.
- The following options are also configured in the Dynamic Ports section of the Firewall Settings | Advanced page.
Enable support for Oracle (SQLNet) - Select if you have Oracle applications on your network.
Enable RTSP Transformations - Select this option to support on-demand delivery of real time data, such as audio and video. RTSP (Real Time Streaming Protocol) is an application level protocol for control over delivery of data with real-time properties.
Source Routed Packets
- Drop Source Routed Packets - (Enabled by default.) Clear this check box if you are testing traffic between two specific hosts and you are using source routing.
Connections
The Connections section provides the ability to fine-tune the performance of the appliance to prioritize either optimal performance or support for an increased number of simultaneous connections that are inspected by firewall services. There is no change in the level of security protection provided by either of the DPI Connections settings below. The following connection options are available:
- Maximum SPI Connections (DPI services disabled) - This option does not provide SonicWall DPI Security Services protection and optimizes the firewall for maximum number of connections with only Stateful packet inspection enabled.
- Maximum DPI Connections (DPI services enabled) - This is the default and recommended setting for most SonicWall deployments.
- DPI Connections (DPI services enabled with additional performance optimization) - This option is intended for performance critical deployments. This option trades off the number of maximum DPI connections for an increased firewall DPI inspection throughput.
The maximum number of connections also depends on whether App Flow is enabled and if an external collector is configured, as well as the physical capabilities of the particular model of SonicWall security appliance. Mousing over the question mark icon next to the Connections heading displays a pop-up table of the maximum number of connections for your specific SonicWall security appliance for the various configuration permutations. The
table entry for your current configuration is indicated in the table, as shown in the example below.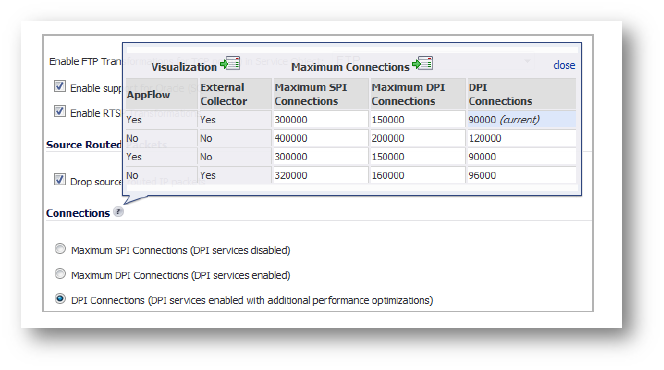
Access Rule Service Options
- Force inbound and outbound FTP data connections to use default port 20 - The default configuration allows FTP connections from port 20 but remaps outbound traffic to a port such as 1024. If the check box is selected, any FTP data connection through the security appliance must come from port 20 or the connection is dropped. The event is then logged as a log event on the security appliance.
- Apply firewall rules for intra-LAN traffic to/from the same interface - Applies firewall rules that is received on a LAN interface and that is destined for the same LAN interface. Typically, this only necessary when secondary LAN subnets are configured.
- IP and UDP Checksum Enforcement:
- Enable IP header checksum enforcement - Select this to enforce IP header checksums.
- Enable UDP checksum enforcement - Select this to enforce IP header checksums.
IPv6 Advanced Configuration
- Drop IPv6 Routing Header type 0 packets V Select this to prevent a potential DoS attack that exploits IPv6 Routing Header type 0 (RH0) packets. When this setting is enabled, RH0 packets are dropped unless their destination is the SonicWall security appliance and their Segments Left value is 0. Segments Left specifies the number of route segments remaining before reaching the final destination.