How can I configure Port Address Translation (PAT) or Port redirection?
Description
This article describes how to change Incoming or outgoing ports for any traffic flow that goes through the SonicWall. This process is also known as PAT'ing or Port Address Translation (PAT).
For this process the device can be any of the following:
- Web Server
- FTP Server
- Email Server
- Terminal Server
- DVR (Digital Video Recorder)
- PBX
- SIP Server
- IP Camera
- Printer
- Application Server
- Any custom Server Roles
- Game Consoles
Don't want to read? Watch instead!
Manually translating Ports from a host on the Internet to a server, or vice versa, behind the SonicWall using SonicOS involves the following steps:
- Creating the necessary Address Objects.
- Creating the necessary Service Objects.
- Creating the appropriate PAT Policies which can include Inbound, Outbound, and Loopback.
- Creating the necessary Firewall Access Rules.
These steps will also allow you to enable port address translation with or without altering the IP addresses involved. If you'd also like to alter the IPs via Network Address Translation (NAT) please see How to Enable Port Forwarding and Allow Access to a Server Through the SonicWall.
 TIP: The public server wizard is a straightforward and simple way to setup Port Address Translation through the SonicWall. The public server wizard will simplify the above three steps by prompting your for information and creating the necessary settings automatically.
TIP: The public server wizard is a straightforward and simple way to setup Port Address Translation through the SonicWall. The public server wizard will simplify the above three steps by prompting your for information and creating the necessary settings automatically.
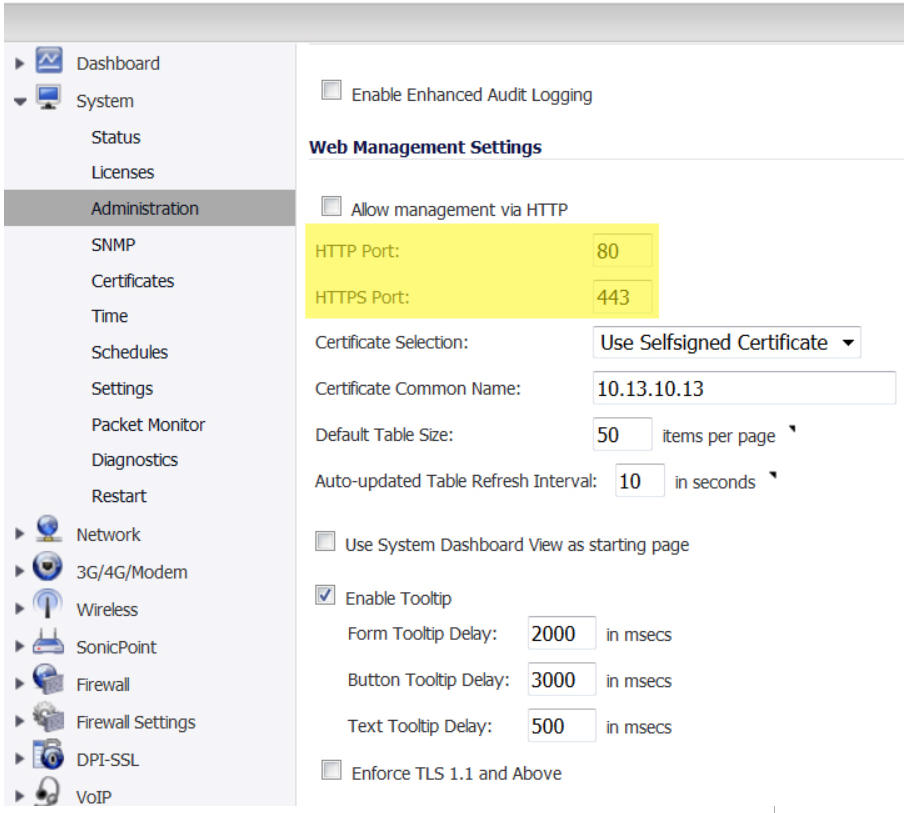
 CAUTION: The SonicWall security appliance is managed by HTTP (Port 80) and HTTPS (Port 443), with HTTPS management being enabled by default. If you are using one or more of the WAN IP addresses for HTTP/HTTPS port forwarding to a server then you must change the management Port to an unused Port, or change the Port when navigating to your server via NAT or another method.
CAUTION: The SonicWall security appliance is managed by HTTP (Port 80) and HTTPS (Port 443), with HTTPS management being enabled by default. If you are using one or more of the WAN IP addresses for HTTP/HTTPS port forwarding to a server then you must change the management Port to an unused Port, or change the Port when navigating to your server via NAT or another method.
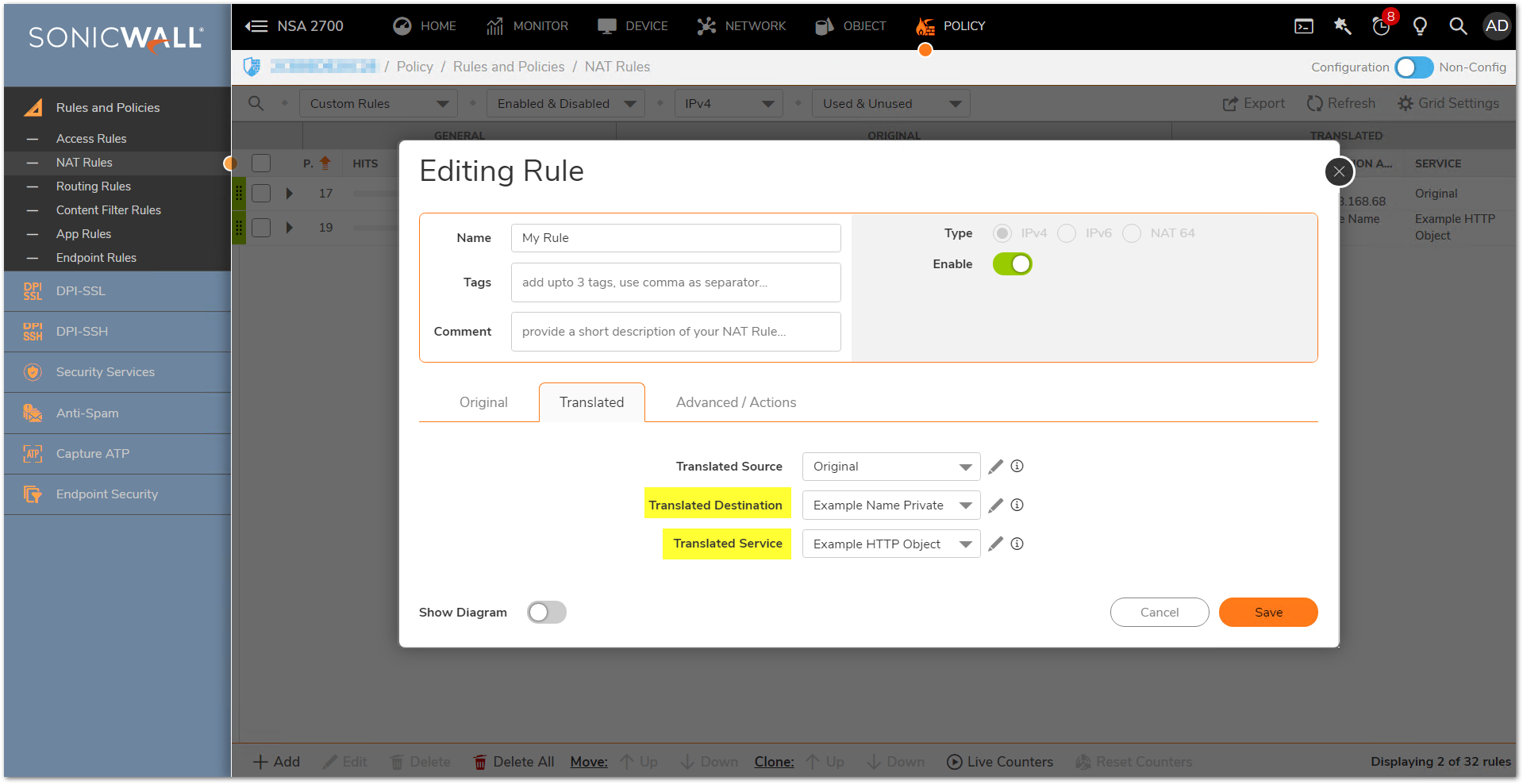
The following snapshot is from SonicOS 7.x
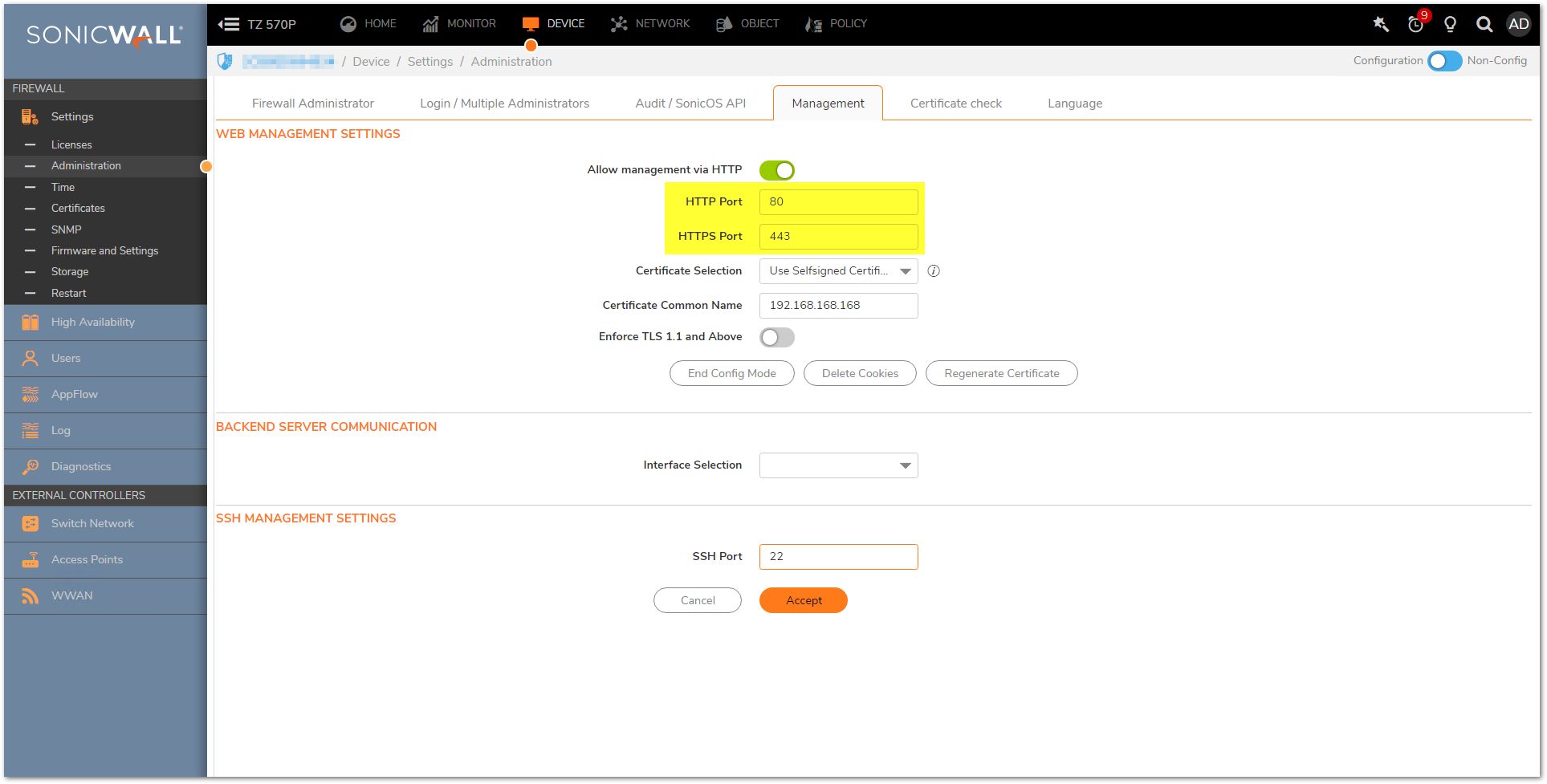
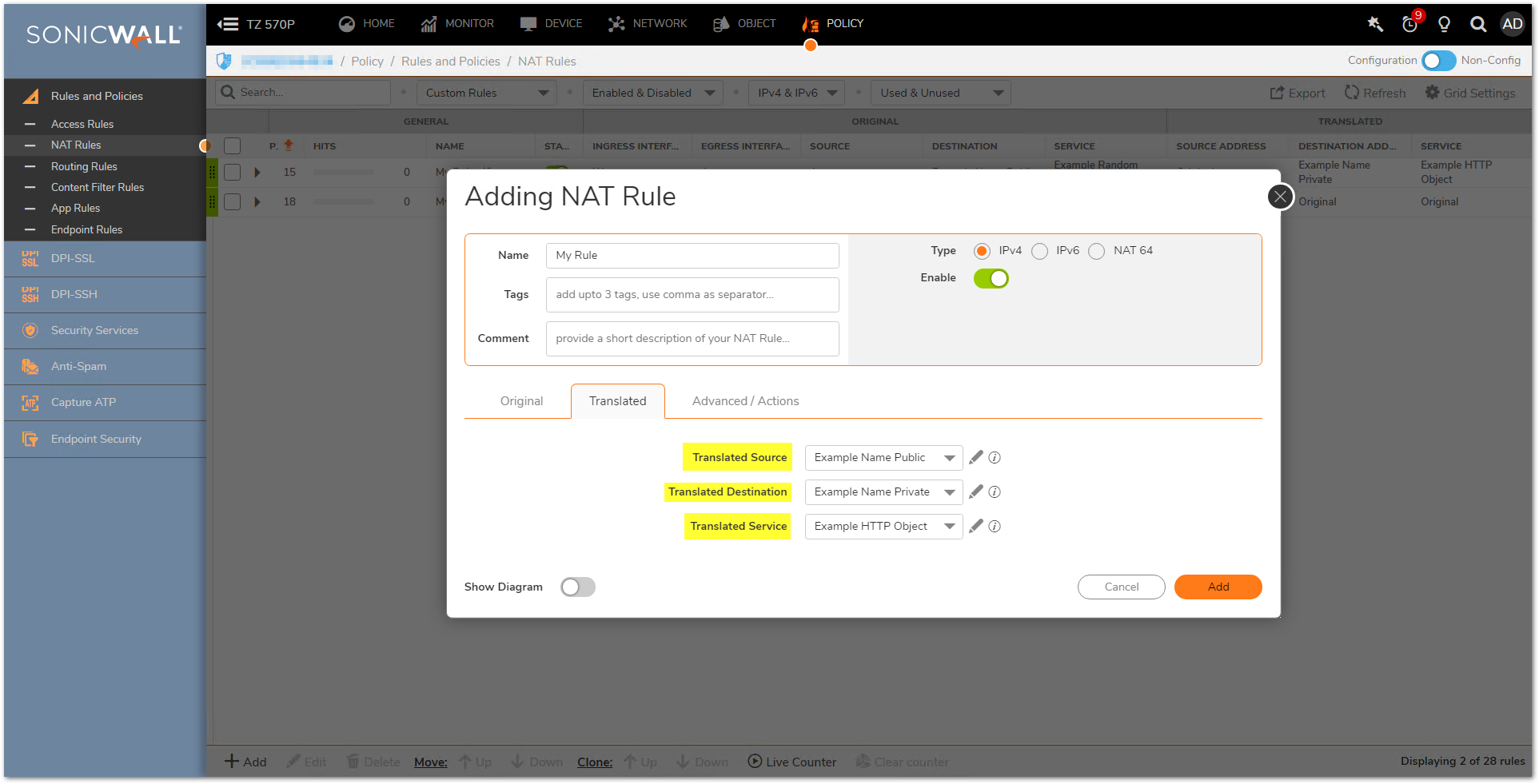
The following snapshot is from SonicOS 6.x
Resolution
Resolution for SonicOS 7.X
This release includes significant user interface changes and many new features that are different from the SonicOS 6.5 and earlier firmware. The below resolution is for customers using SonicOS 7.X firmware.
The following walk-through details a request on port 4000 coming into the SonicWall via the WAN and being forwarded to a server on the LAN as Port 80 (HTTP). Once the configuration is complete, Internet Users can access the server via port 4000. Although the examples below show the LAN Zone and HTTP (Port 80) they can apply to any zone and any port that is required. Similarly, the WAN IP address can be replaced with any Public IP that is routed to the SonicWall, such as a public range provided by an ISP.
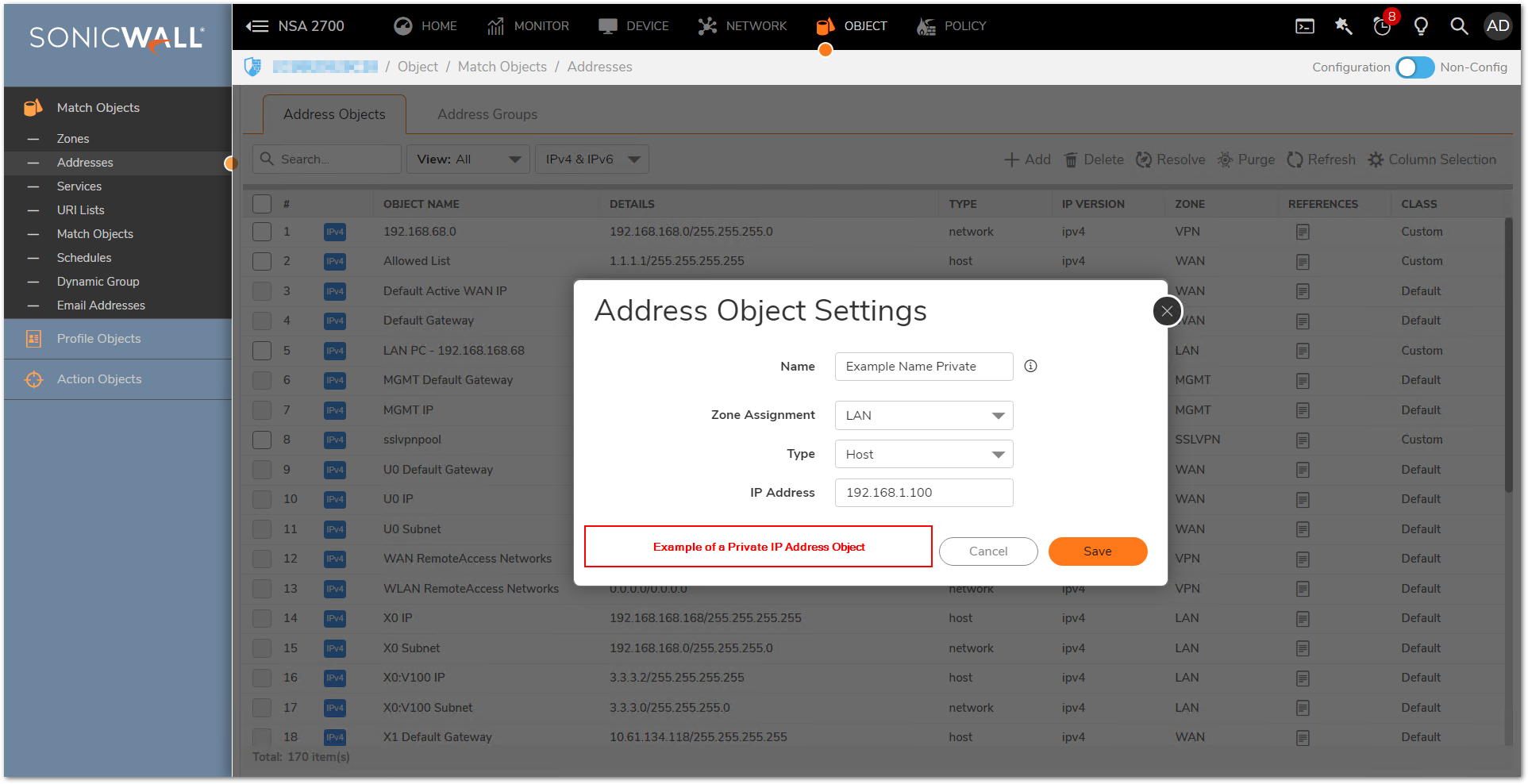
Creating the two Address Objects
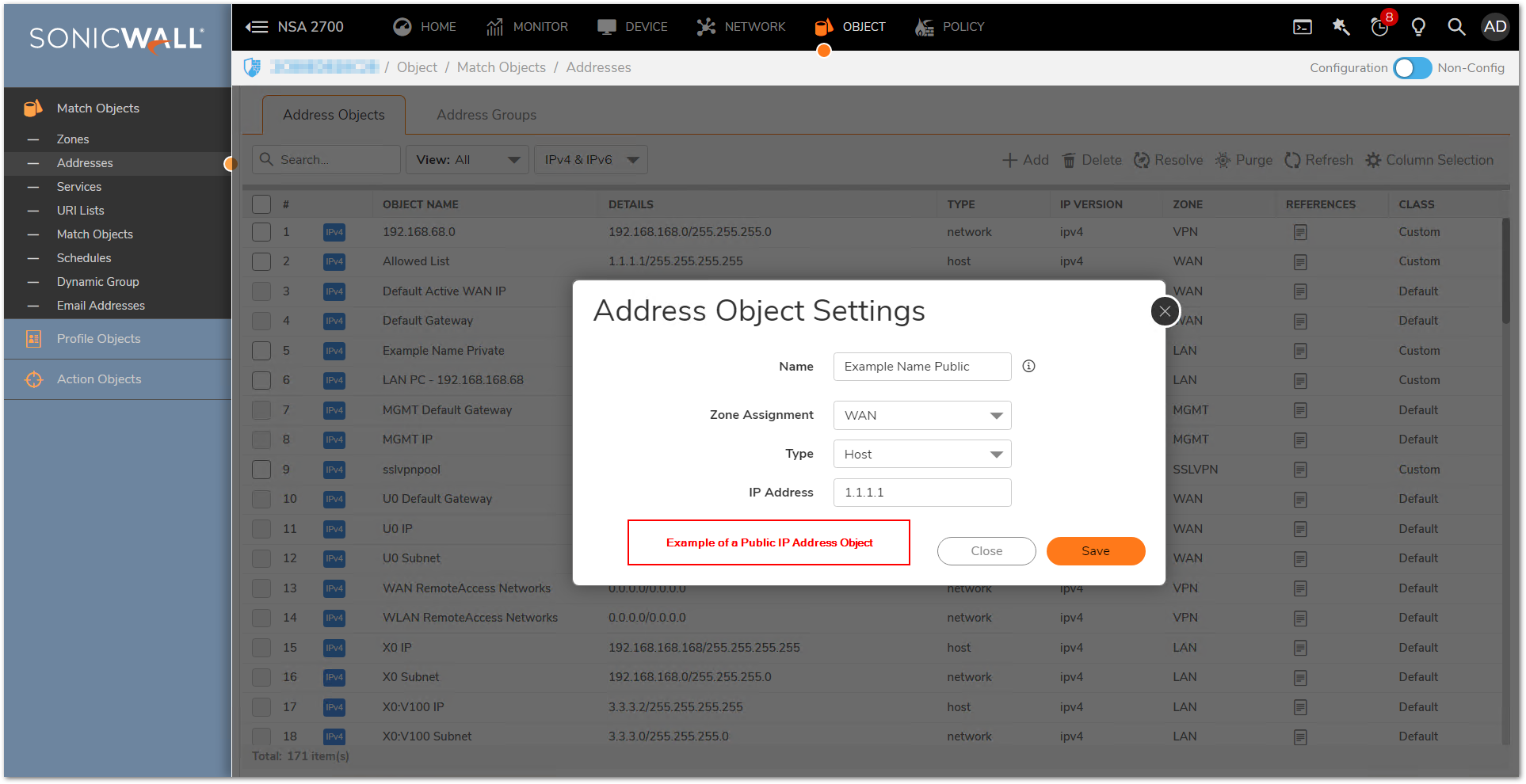
1-Created the necessary private Address Objects.
- Log into the SonicWall GUI.
- Click OBJECT in the top navigation menu.
- Click Match Objects | Addresses.
- Click Add button and create one address objects for the server's private IP.
- Click Save.
2-Created the necessary public Address Objects.
- Click Add button and create one address objects for the server's public IP.
- Click Save.
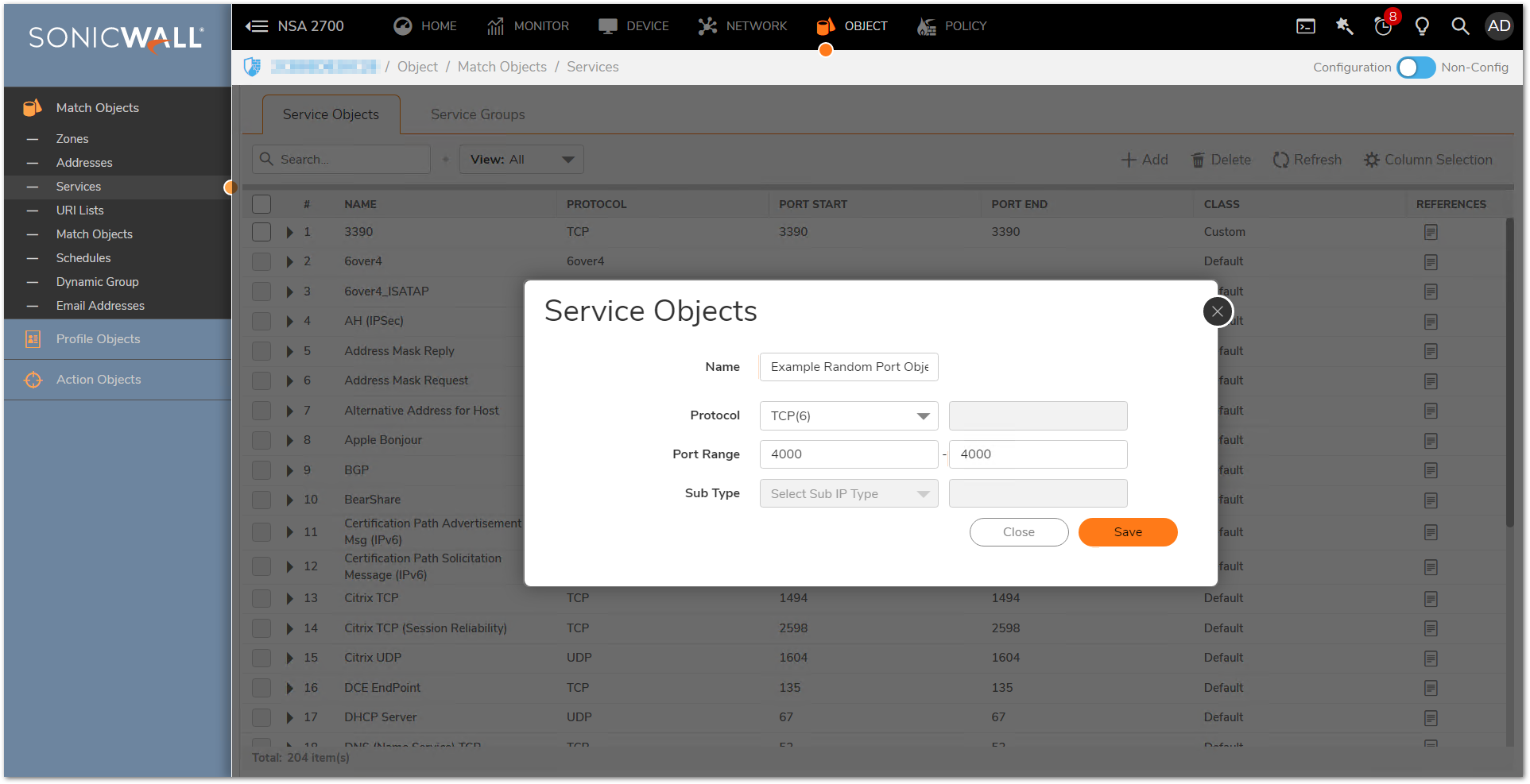
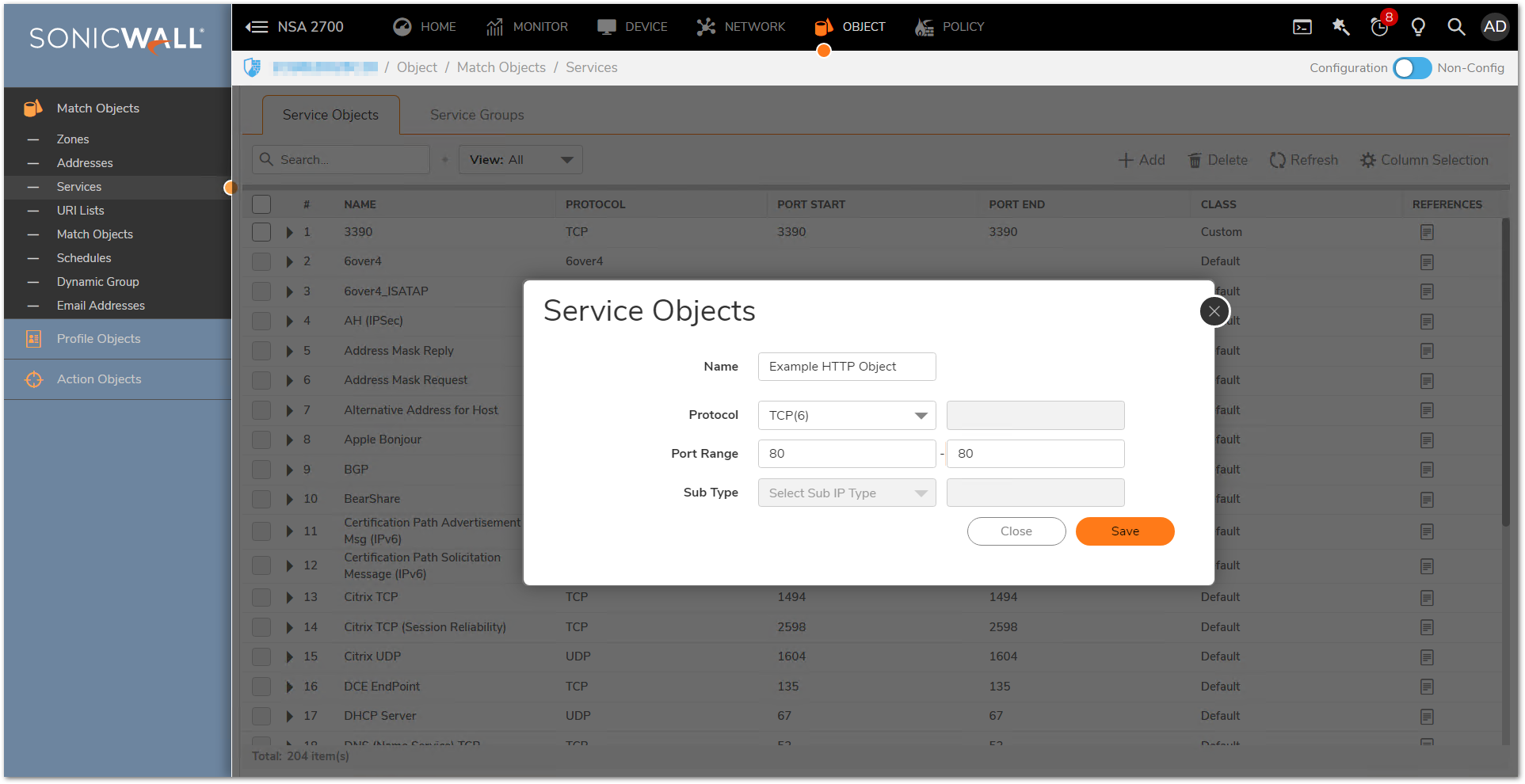
3-Creating the necessary Service Object
- Click OBJECT in the top navigation menu.
- Click Match Objects | Services.
- Click Add button and create the necessary service objects for the ports required.
- Ensure that you know the correct protocol for the service object (TCP, UDP, etc.). If you're unsure of which protocol is in use, perform a Packet Capture.
- Click Save.
4-Creating the appropriate PAT Policies which can include Inbound, Outbound, and Loopback
To allow access to a local server from outside, will require creating two the appropriate NAT Policies; Inbound and Outbound .
A NAT Policy will allow SonicOS to translate incoming packets destined for a public IP address to a private IP address, and/or a specific port to another specific port. Every packet contains information about the Source and Destination IP addresses and ports and with a NAT policy SonicOS can examine packets and rewrite those addresses and ports for incoming and outgoing traffic.
- Click POLICY in the top navigation menu.
- Click Rules and Policies | NAT Rules.
- Click Add button and a pop-up window will appear.
- Click Save to add the NAT Policy to the SonicWall NAT policy table.
 NOTE: When creating a NAT policy you may select the "Create a reflexive policy" checkbox". This will create an inverse policy automatically, in the example below adding a reflexive policy for the NAT Policy for inbound connections will also create the NAT Policy for outbound connections. This option is not available when configuring an existing NAT policy, only when creating a new policy.
NOTE: When creating a NAT policy you may select the "Create a reflexive policy" checkbox". This will create an inverse policy automatically, in the example below adding a reflexive policy for the NAT Policy for inbound connections will also create the NAT Policy for outbound connections. This option is not available when configuring an existing NAT policy, only when creating a new policy.
1.The following example is a NAT Policy for inbound connections,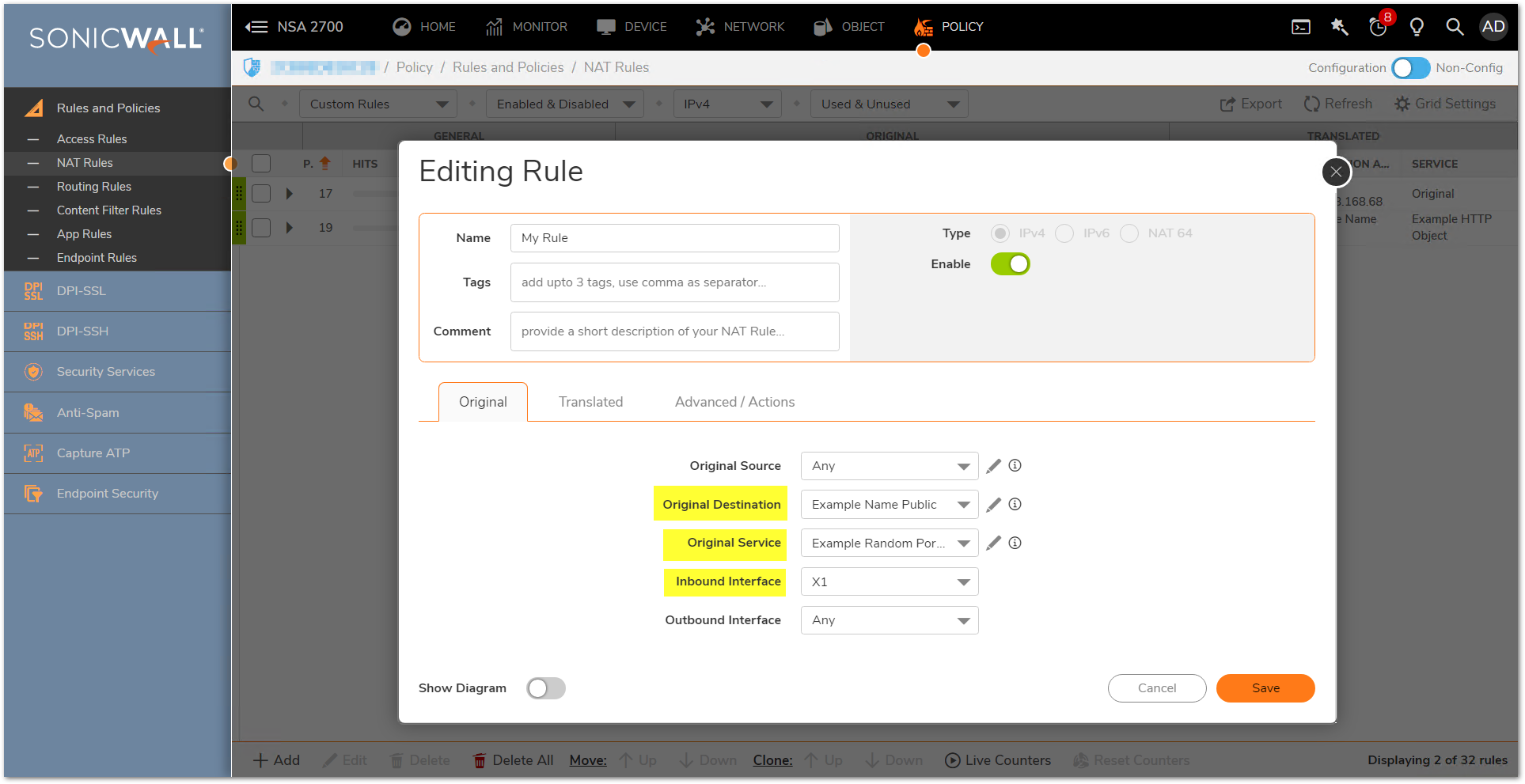
2.The following example is a NAT Policy for outbound connections,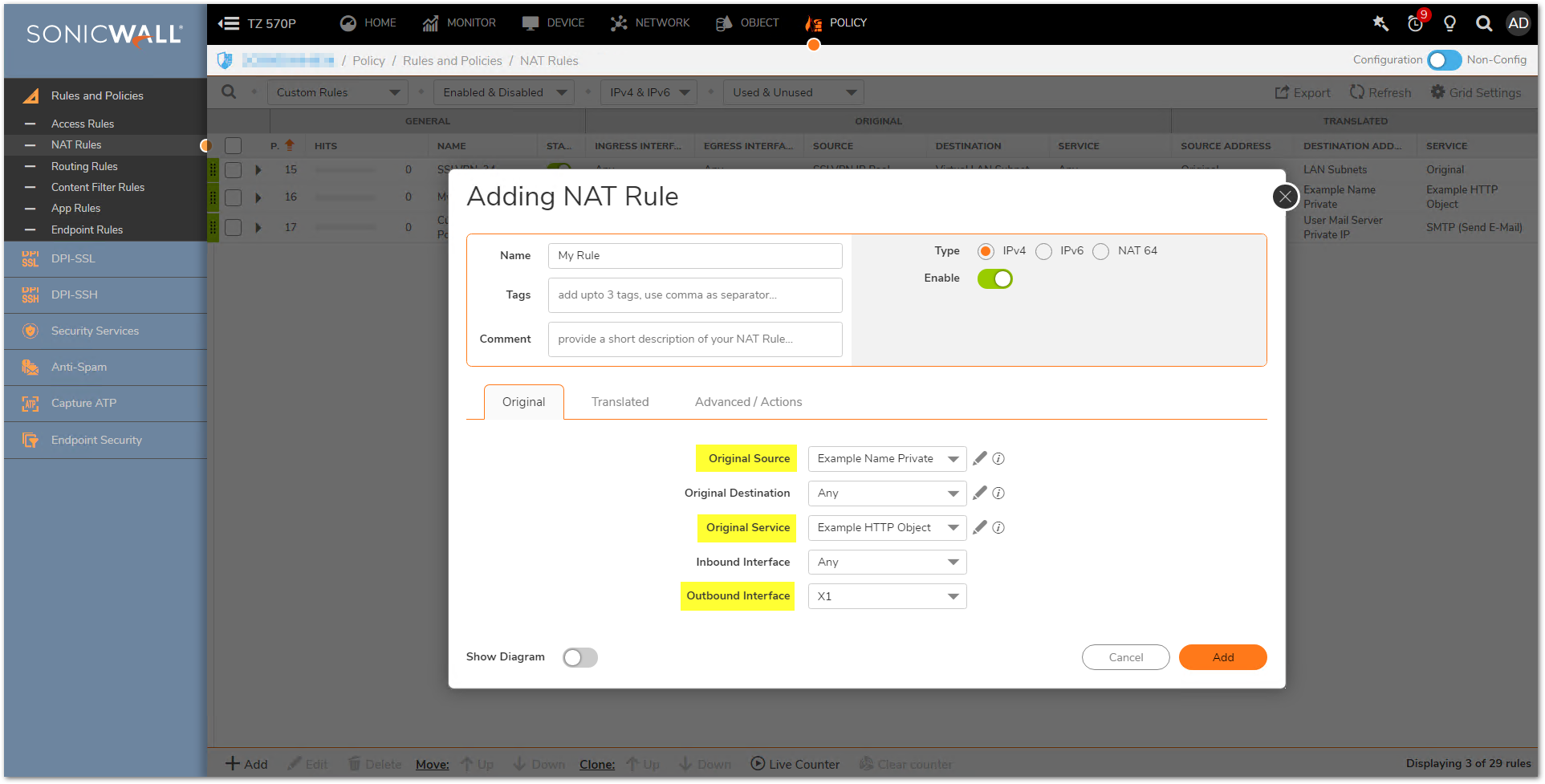

Loopback NAT Policy
A Loopback NAT Policy is required when Users on the local LAN/WLAN need to access an internal server via its public IP/Public DNS name. This policy will loopback the users request for access as coming from the public IP of the WAN and then translate down to the private IP of the server. Without a Loopback NAT policy internal Users will be forced to use the private IP of the server to access it which will typically create problems with DNS.
If you wish to access this server from other internal zones using the public IP address http://1.1.1.1 consider creating a Loopback NAT Policy:
- Original Source: Firewall Subnets
- Translated Source: Example Name Public
- Original Destination: Example Name Public
- Translated Destination: Example Name Private
- Original Service: Example Random Port Object
- Translated Service: Example HTTP Object
- Inbound Interface: Any
- Outbound Interface: Any
- Comment: Loopback Policy
- Enable NAT Policy: Checked
- Create a reflexive policy: Unchecked

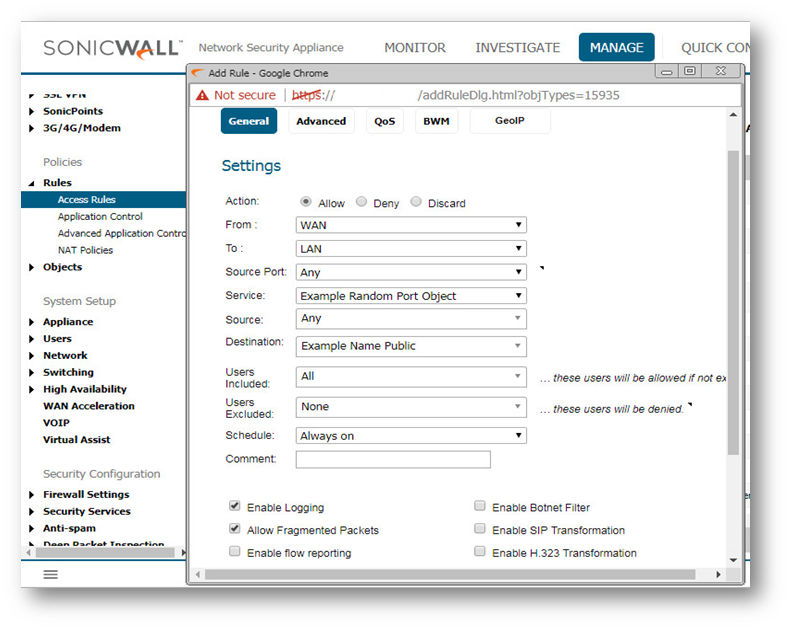
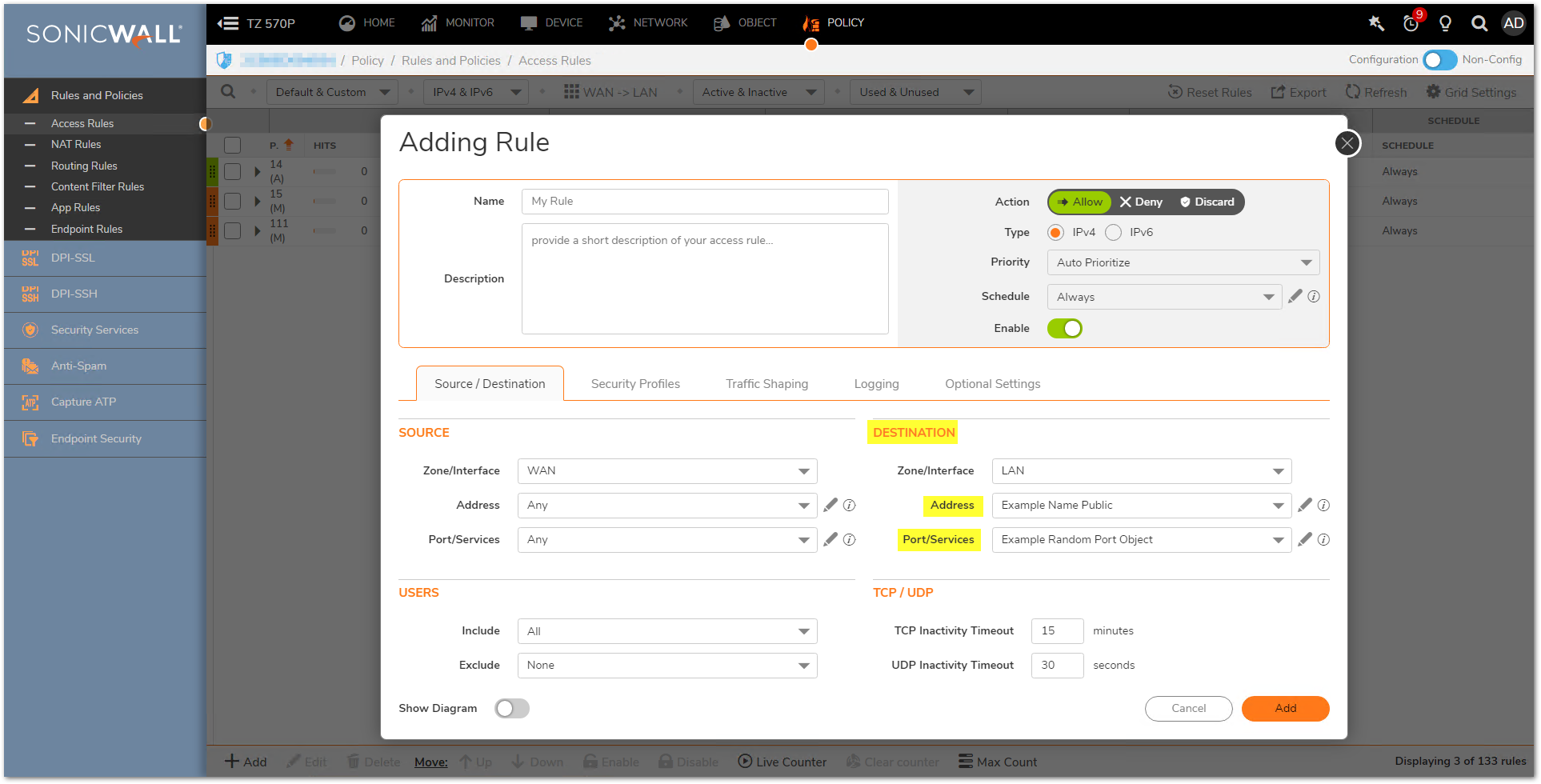
5-Creating the necessary Firewall Access Rules
- Click POLICY in the top navigation menu.
- Click Rules and Policies | Access Rules.
- Select the View Type as Matrix and select your WAN to Appropriate Zone Access Rule. (This will be the zone the private IP of the server resides on.)
- Click Add button and in the pop-up window create the required access rule by configuring the fields as shown below.
- Click Add .
Resolution for SonicOS 6.5
This release includes significant user interface changes and many new features that are different from the SonicOS 6.2 and earlier firmware. The below resolution is for customers using SonicOS 6.5 firmware.
The following walk-through details a request on port 4000 coming into the SonicWall via the WAN and being forwarded to a server on the LAN as Port 80 (HTTP). Once the configuration is complete, Internet Users can access the server via port 4000. Although the examples below show the LAN Zone and HTTP (Port 80) they can apply to any zone and any port that is required. Similarly, the WAN IP address can be replaced with any Public IP that is routed to the SonicWall, such as a public range provided by an ISP.
 TIP: If your user interface looks different to the screenshots in this article, you may need to upgrade your firmware to the latest firmware version for your appliance. To learn more about upgrading firmware, please see Procedure to Upgrade the SonicWall UTM Appliance Firmware Image with Current Preferences.
TIP: If your user interface looks different to the screenshots in this article, you may need to upgrade your firmware to the latest firmware version for your appliance. To learn more about upgrading firmware, please see Procedure to Upgrade the SonicWall UTM Appliance Firmware Image with Current Preferences.
Creating the necessary Address Objects
- Log into the SonicWall GUI.
- Click Manage in the top navigation menu.
- Click Objects| Address Objects.
- Click Add a new Address object button and create two address objects for the server's public IP and the server's private IP.
- Click OK .

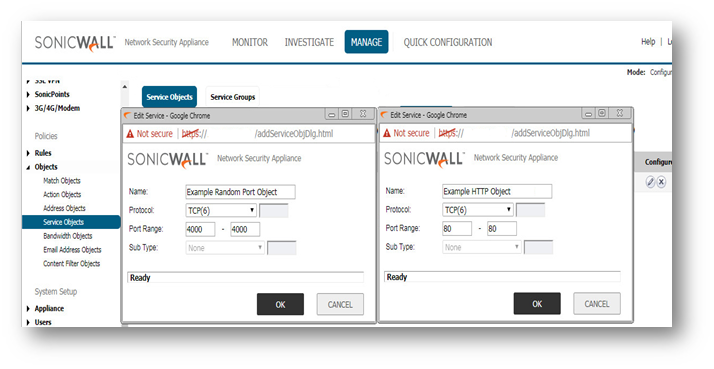
Creating the necessary Service Object
- Click Manage in the top navigation menu.
- Click Objects | Service Objects.
- Click Add a new Service object button and create the necessary service objects for the ports required.
- Ensure that you know the correct protocol for the service object (TCP, UDP, etc.). If you're unsure of which protocol is in use, perform a Packet Capture.
- Click OK .
Creating the appropriate PAT Policies which can include Inbound, Outbound, and Loopback
A NAT Policy will allow SonicOS to translate incoming packets destined for a public IP address to a private IP address, and/or a specific port to another specific port. Every packet contains information about the Source and Destination IP addresses and ports and with a NAT policy SonicOS can examine packets and rewrite those addresses and Ports for incoming and outgoing traffic.
- Click Manage in the top navigation menu.
- Click Rules | NAT Policies.
- Click Add a new NAT Policy button and a pop-up window will appear.
- Click Add to add the NAT Policy to the SonicWall NAT policy table.
 NOTE: When creating a NAT policy you may select the "Create a reflexive policy" checkbox". This will create an inverse policy automatically, in the example below adding a reflexive policy for the NAT Policy on the left will also create the NAT Policy on the right. This option is not available when configuring an existing NAT policy, only when creating a new policy.
NOTE: When creating a NAT policy you may select the "Create a reflexive policy" checkbox". This will create an inverse policy automatically, in the example below adding a reflexive policy for the NAT Policy on the left will also create the NAT Policy on the right. This option is not available when configuring an existing NAT policy, only when creating a new policy.
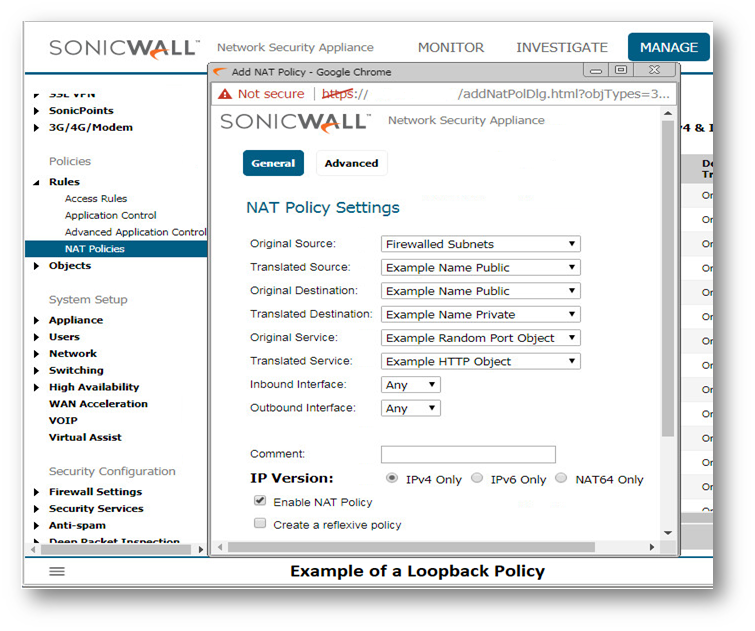
Loopback NAT Policy
A Loopback NAT Policy is required when Users on the local LAN/WLAN need to access an internal server via its public IP/Public DNS name. This policy will loopback the users request for access as coming from the public IP of the WAN and then translate down to the private IP of the server. Without a Loopback NAT policy internal Users will be forced to use the private IP of the server to access it which will typically create problems with DNS.
If you wish to access this server from other internal zones using the public IP address Http://1.1.1.1 consider creating a Loopback NAT Policy:
- Original Source: Firewalled Subnets
- Translated Source: Example Name Public
- Original Destination: Example Name Public
- Translated Destination: Example Name Private
- Original Service: Example Random Port Object
- Translated Service: Example HTTP Object
- Inbound Interface: Any
- Outbound Interface: Any
- Comment: Loopback Policy
- Enable NAT Policy: Checked
- Create a reflexive policy: Unchecked
Creating the necessary Firewall Access Rules
- Click Manage in the top navigation menu.
- Click Rules| Access Rules.
- Select the View Type as Matrix and select your WAN to Appropriate Zone Access Rule. (This will be the zone the private IP of the server resides on.)
- Click Add a new entry/Add button and in the pop-up window create the required access rule by configuring the fields as shown below.
- Click Add .