-
Products
-
SonicPlatform
SonicPlatform is the cybersecurity platform purpose-built for MSPs, making managing complex security environments among multiple tenants easy and streamlined.
Discover More
-
-
Solutions
-
Federal
Protect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn MoreFederalProtect Federal Agencies and Networks with scalable, purpose-built cybersecurity solutions
Learn More - Industries
- Use Cases
-
-
Partners
-
Partner Portal
Access to deal registration, MDF, sales and marketing tools, training and more
Learn MorePartner PortalAccess to deal registration, MDF, sales and marketing tools, training and more
Learn More - SonicWall Partners
- Partner Resources
-
-
Support
-
Support Portal
Find answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn MoreSupport PortalFind answers to your questions by searching across our knowledge base, community, technical documentation and video tutorials
Learn More - Support
- Resources
- Capture Labs
-
- Company
- Contact Us
Can SonicWall firewalls prevent brute force attacks?



Description
This article describes how to protect the firewall and the network behind it from bruteforce or dictionary attacks.
A brute force attack is a method used to obtain information such as a user password or personal identification number (PIN) by trying thousands of combinations. In a brute force attack, automated software is used to generate a large number of consecutive guesses as to the value of the desired data.
A dictionary attack is a method of using a dictionary in order to get access to a computer or server by systematically entering every word in a dictionary as a password. It can also be used to decrypt encrypted messages by guessing the key.
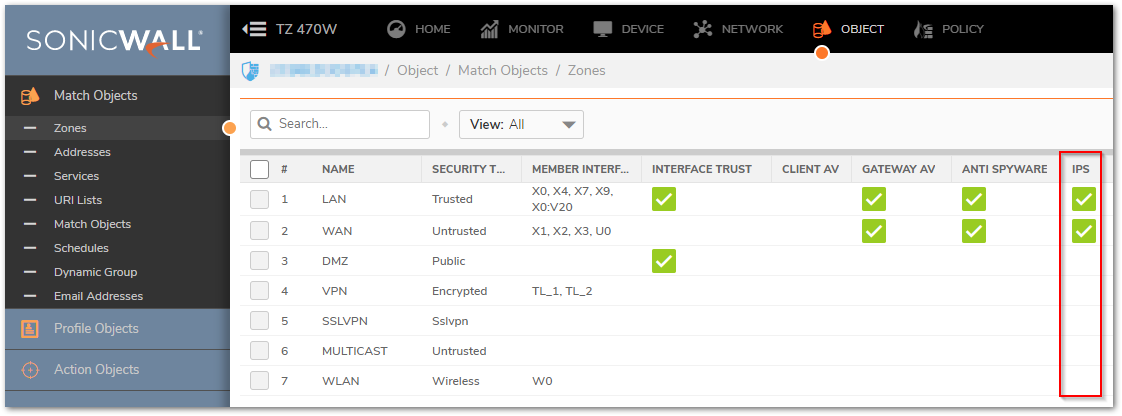
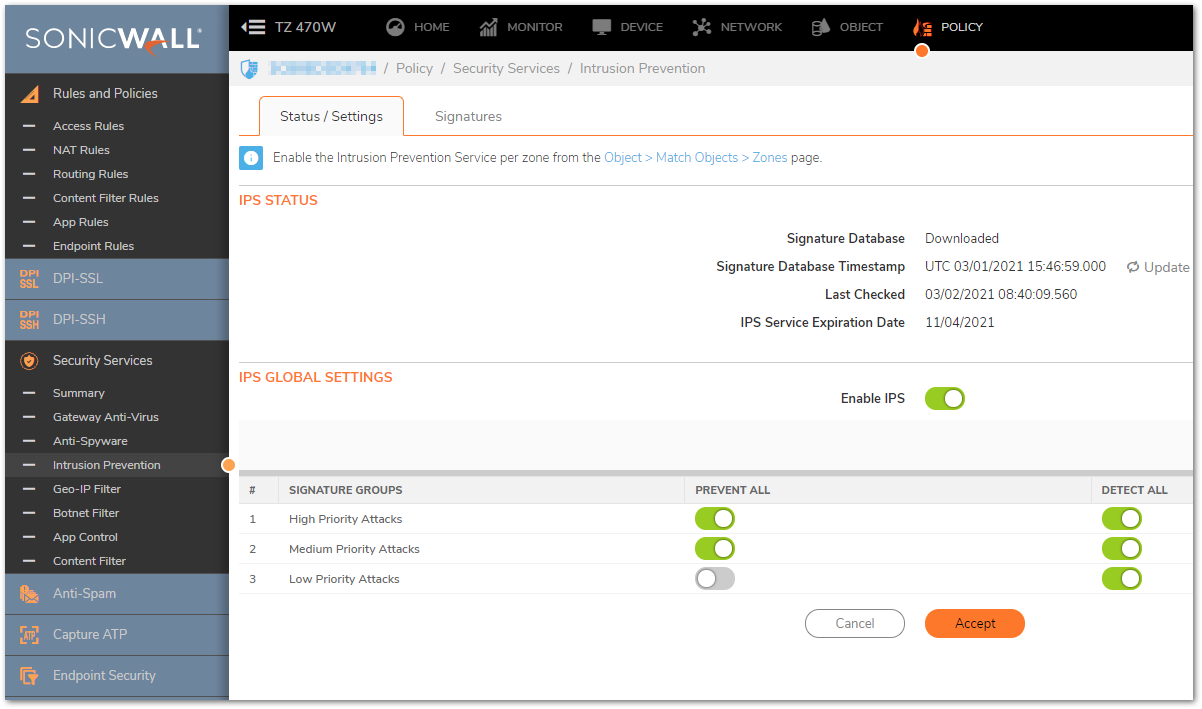
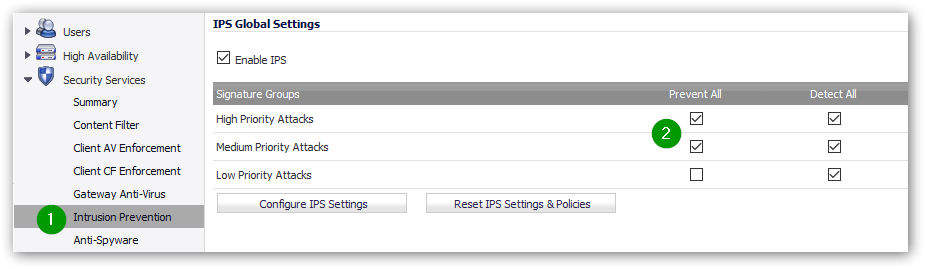
The Intrusion Prevention System (IPS) available in the SonicWall, if enabled on the WAN zone, should prevent most of the exploits, web attacks, SQL injections and database attacks. In order to prevent them, the SonicWall will match the traffic pattern against the IPS signatures and if it matches the traffic will be blocked.
 NOTE: IPS must be licensed and the signatures must be up-to-date.
NOTE: IPS must be licensed and the signatures must be up-to-date.
Some bruteforce attacks are not easy to detect as they look like normal attempts to login.
Resolution
Resolution for SonicOS 7.X
This release includes significant user interface changes and many new features that are different from the SonicOS 6.5 and earlier firmware. The below resolution is for customers using SonicOS 7.X firmware.
- Make sure IPS is licensed and enabled from POLICY | Security Services | Intrusion Prevention and on the WAN zone from OBJECT | Match Objects | Zones. You will need to make sure that the database is correctly downloaded and there's nothing blocking the updates.
- Ensure that IPS is preventing (blocking) med/high attacks.
 NOTE: DPI-SSL should also be licensed and configured so attacks via HTTPS/SSH can be easily detected:
NOTE: DPI-SSL should also be licensed and configured so attacks via HTTPS/SSH can be easily detected:
- Enabling Geo-IP and Botnet Filter security services can also help prevent brute force attacks.
- Enable TCP, UDP, ICMP Flood Protection on NETWORK | Firewall | Flood Protection.
- If you wish to have access to the WAN Interface via SSH or HTTPS, you may create an access rule (POLICY | Rules and Policies | Access Rules) from WAN to WAN denying all traffic but the HTTPS/SSH traffic from specific Public IPs of your
- On DEVICE | Settings | Administration
- enable Enable Administrator/user lockout.
- enable Password must be changed every (days).
- enable Bar repeated passwords for this many changes.
- Set the Enforce password complexity: to Require alphabetic, numeric and symbolic characters and set the complexity requirements.
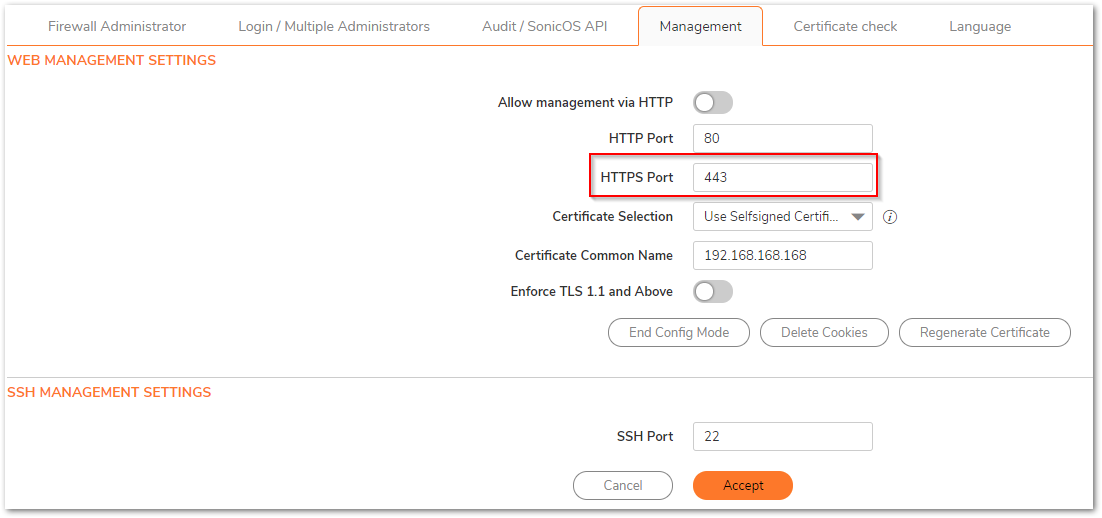
- Change the default HTTPS and SSH Ports for management 443 to a custom one.
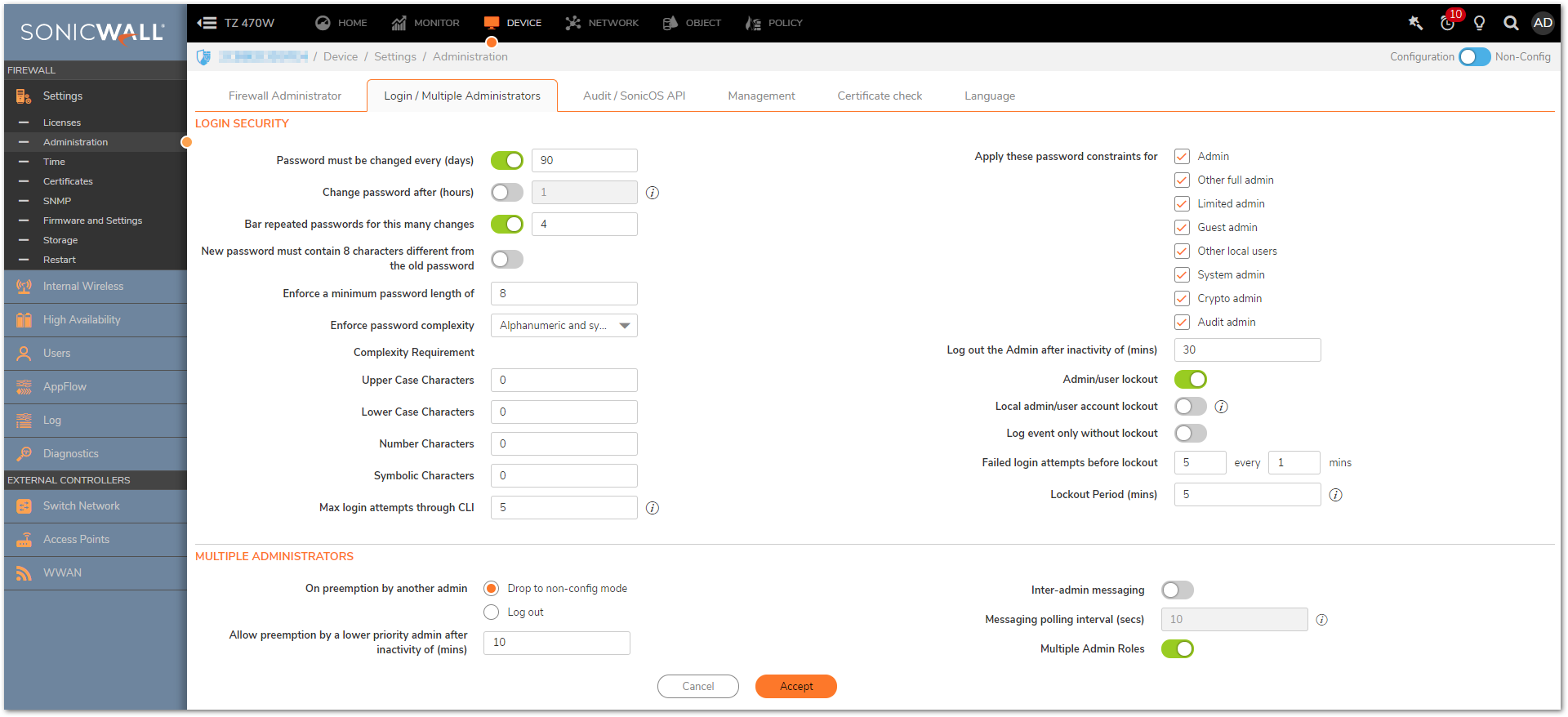
 CAUTION: Be very careful about enabling the "administrator/user lockout"! Some bruteforce attacks are actually DoS, attackers are just trying to lockout a huge number of your most important users so that your network will be down.
CAUTION: Be very careful about enabling the "administrator/user lockout"! Some bruteforce attacks are actually DoS, attackers are just trying to lockout a huge number of your most important users so that your network will be down.
- Use VPNs (SSLVPN or IPSec VPN) to secure access to internal servers should you need RDP or get access to them.You shouldn't open ports like RDP - 3389 to the whole world using a NAT Policy unless you're filtering the access via access rules to only known Public IPs.
- Do not use the option Use default key for simple client provisioning or Cache XAUTH User Name and Password on Client: on the VPN | Settings and use Strong Encryption Methods.
- Enable the 2 Factors Authentication for external connecting users (i.e. SSLVPN or GVC users): when creating Local Users from Users | Local Users, enable the option Require one-time passwords or enable it on your LDAP/Radius Servers.
- Bruteforce/Dictionary attacks via SSLVPN can be blocked by using a SonicWall SRA appliance: How to block Brute Force and Dictionary attacks with SRA.
 CAUTION: Accomplishing the best protection for your network against bruteforce and dictionary attacks would require the upstream ISP or services like CloudFlare, Incapsula, etc. to drop the traffic once a bruteforce attack against your network is detected.
CAUTION: Accomplishing the best protection for your network against bruteforce and dictionary attacks would require the upstream ISP or services like CloudFlare, Incapsula, etc. to drop the traffic once a bruteforce attack against your network is detected.
Resolution for SonicOS 6.5
This release includes significant user interface changes and many new features that are different from the SonicOS 6.2 and earlier firmware. The below resolution is for customers using SonicOS 6.5 firmware.
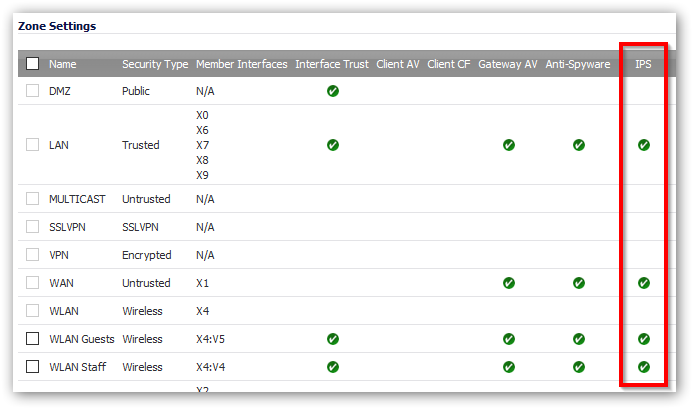
- Make sure IPS is licensed and enabled from Manage | Security Services | Intrusion Prevention and on the WAN zone from Manage | Network | Zones. You will need to make sure that the database is correctly downloaded and there's nothing blocking the updates.
- Ensure that IPS is preventing (blocking) med/high attacks.
 NOTE: DPI-SSL should also be licensed and configured so attacks via HTTPS/SSH can be easily detected:
NOTE: DPI-SSL should also be licensed and configured so attacks via HTTPS/SSH can be easily detected: - Enabling Geo-IP and Botnet Filter security services can also help prevent brute force attacks.
- Enable TCP, UDP, ICMP Flood Protection on Manage | Firewall Settings | Flood Protection.
- If you wish to have access to the WAN Interface via SSH or HTTPS, you may create an access rule (Manage | Rules | Access Rules) from WAN to WAN denying all traffic but the HTTPS/SSH traffic from specific Public IPs of your company.
- On Manage | Appliance | Base Settings
- enable Enable administrator/user lockout.
- enable Password must be changed every (days).
- enable Bar repeated passwords for this many changes.
- Set the Enforce password complexity: to Require alphabetic, numeric and symbolic characters and set the complexity requirements.
- Change the default HTTPS and SSH Ports for management 443 to a custom one.
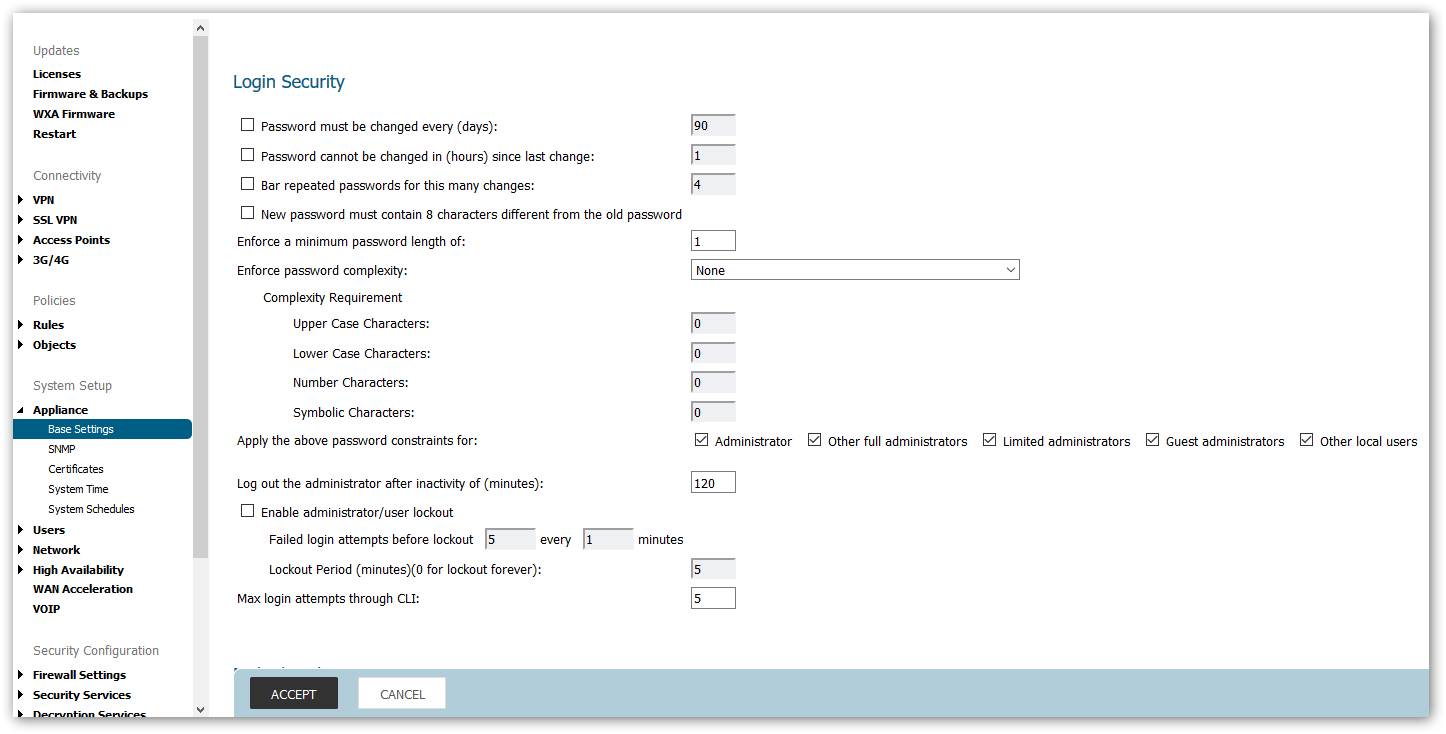
 CAUTION: Be very careful about enabling the administrator/user lockout! Some bruteforce attacks are actually DoS, attackers are just trying to lockout a huge number of your most important users so that your network will be down.
CAUTION: Be very careful about enabling the administrator/user lockout! Some bruteforce attacks are actually DoS, attackers are just trying to lockout a huge number of your most important users so that your network will be down.
- Use VPNs (SSLVPN or IPSec VPN) to secure access to internal servers should you need RDP or get access to them.You shouldn't open ports like RDP - 3389 to the whole world using a NAT Policy unless you're filtering the access via access rules to only known Public IPs.
- Do not use the option Use default key for simple client provisioning or Cache XAUTH User Name and Password on Client: on the Manage | VPN | Base Settings and use Strong Encryption Methods.
- Enable the 2 Factors Authentication for external connecting users (i.e. SSLVPN or GVC users): when creating Local Users from Manage | Users | Local Users & Groups, enable the option Require one-time passwords or enable it on your LDAP/Radius Servers.
- Bruteforce/Dictionary attacks via SSLVPN can be blocked by using a SonicWall SRA appliance: How to block Brute Force and Dictionary attacks with SRA
 CAUTION: Accomplishing the best protection for your network against bruteforce and dictionary attacks would require the upstream ISP or services like CloudFlare, Incapsula, etc. to drop the traffic once a bruteforce attack against your network is detected.
CAUTION: Accomplishing the best protection for your network against bruteforce and dictionary attacks would require the upstream ISP or services like CloudFlare, Incapsula, etc. to drop the traffic once a bruteforce attack against your network is detected.
Resolution for SonicOS 6.2 and Below
The below resolution is for customers using SonicOS 6.2 and earlier firmware. For firewalls that are generation 6 and newer we suggest to upgrade to the latest general release of SonicOS 6.5 firmware.
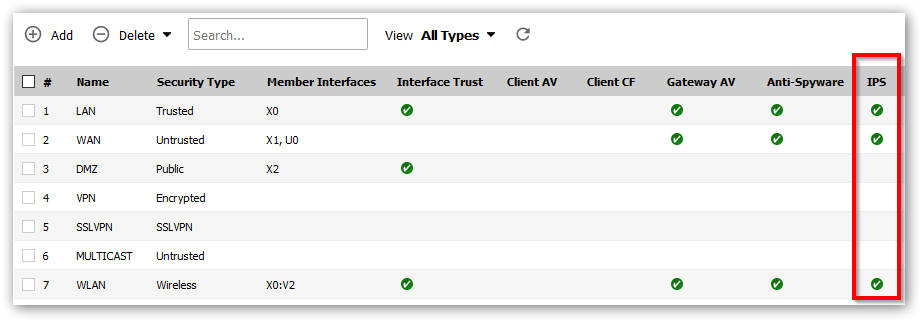
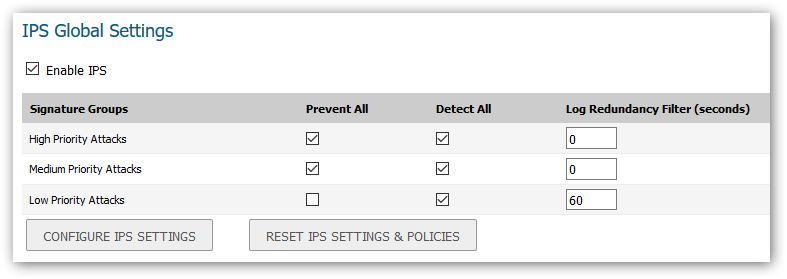
- Make sure IPS is licensed and enabled from Security Services | IPS and on the WAN zone from Network | Zones. You will need to make sure that the database is correctly downloaded and there's nothing blocking the updates.
- Ensure that IPS is preventing (blocking) all med/high attacks.
 NOTE: DPI-SSL should also be licensed and configured so attacks via HTTPS/SSH can be easily detected:
NOTE: DPI-SSL should also be licensed and configured so attacks via HTTPS/SSH can be easily detected: - Geo-IP and Botnet Filter can also help on this fight.
- Enable TCP, UDP, ICMP Flood Protection on Firewall Settings | Flood Protection.
- If you wish to have access to the WAN Interface via SSH or HTTPS, you may create an access rule (Firewall | Access Rules) from WAN to WAN denying all traffic but the HTTPS/SSH traffic from specific Public IPs of your company.
- On System | Administration
- enable Enable administrator/user lockout.
- enable Password must be changed every (days).
- enable Bar repeated passwords for this many changes.
- Set the Enforce password complexity: to Require alphabetic, numeric and symbolic characters and set the complexity requirements.
- Change the default HTTPS and SSH Ports for management 443 to a custom one.
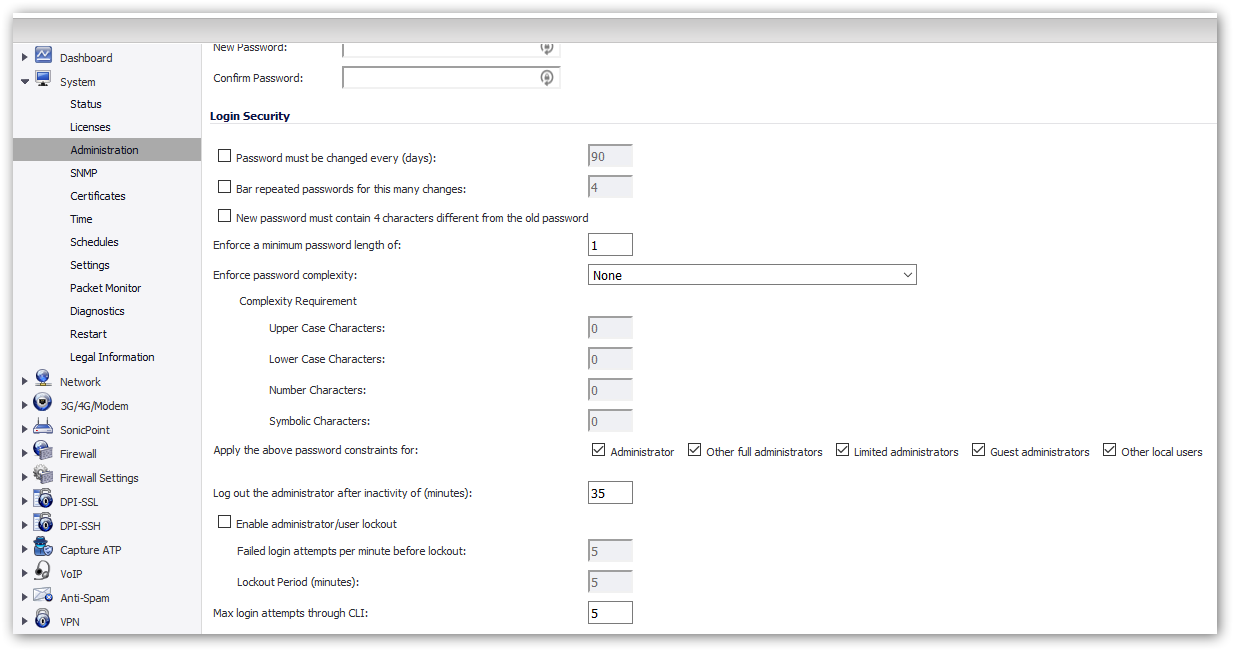
 CAUTION: Be very careful about enabling the "administrator/user lockout"! Some bruteforce attacks are actually DoS, attackers are just trying to lockout a huge number of your most important users so that your network will be down.
CAUTION: Be very careful about enabling the "administrator/user lockout"! Some bruteforce attacks are actually DoS, attackers are just trying to lockout a huge number of your most important users so that your network will be down.
- Use VPNs (SSLVPN or IPSec VPN) to secure access to internal servers should you need RDP or get access to them.You shouldn't open ports like RDP - 3389 to the whole world using a NAT Policy unless you're filtering the access via access rules to only known Public IPs.
- Do not use the option Use default key for simple client provisioning or Cache XAUTH User Name and Password on Client: on the VPN | Settings and use Strong Encryption Methods.
- Enable the 2 Factors Authentication for external connecting users (i.e. SSLVPN or GVC users): when creating Local Users from Users | Local Users, enable the option Require one-time passwords or enable it on your LDAP/Radius Servers.
- Bruteforce/Dictionary attacks via SSLVPN can be blocked by using a SonicWall SRA appliance: How to block Brute Force and Dictionary attacks with SRA.
 CAUTION: Accomplishing the best protection for your network against bruteforce and dictionary attacks would require the upstream ISP or services like CloudFlare, Incapsula, etc. to drop the traffic once a bruteforce attack against your network is detected.
CAUTION: Accomplishing the best protection for your network against bruteforce and dictionary attacks would require the upstream ISP or services like CloudFlare, Incapsula, etc. to drop the traffic once a bruteforce attack against your network is detected.
Related Articles
- How to configure numbered VPN tunnel
- Cysurance Partner FAQ
- How can I enable Enhanced Audit Logging Support?
Categories
- Firewalls > TZ Series > Geo-IP & Botnet Filter
- Firewalls > NSa Series > Geo-IP & Botnet Filter
- Firewalls > TZ Series > IPS/GAV/Spyware
- Firewalls > NSa Series > IPS/GAV/Spyware






 YES
YES NO
NO